- Home
- Resources
- Work samples
- Samples
- Investigation: Secure networks - ABOVE
Digital Technologies
Years 9 and 10
Above satisfactory
Investigation: Secure networks
 1
Annotation 1
1
Annotation 1
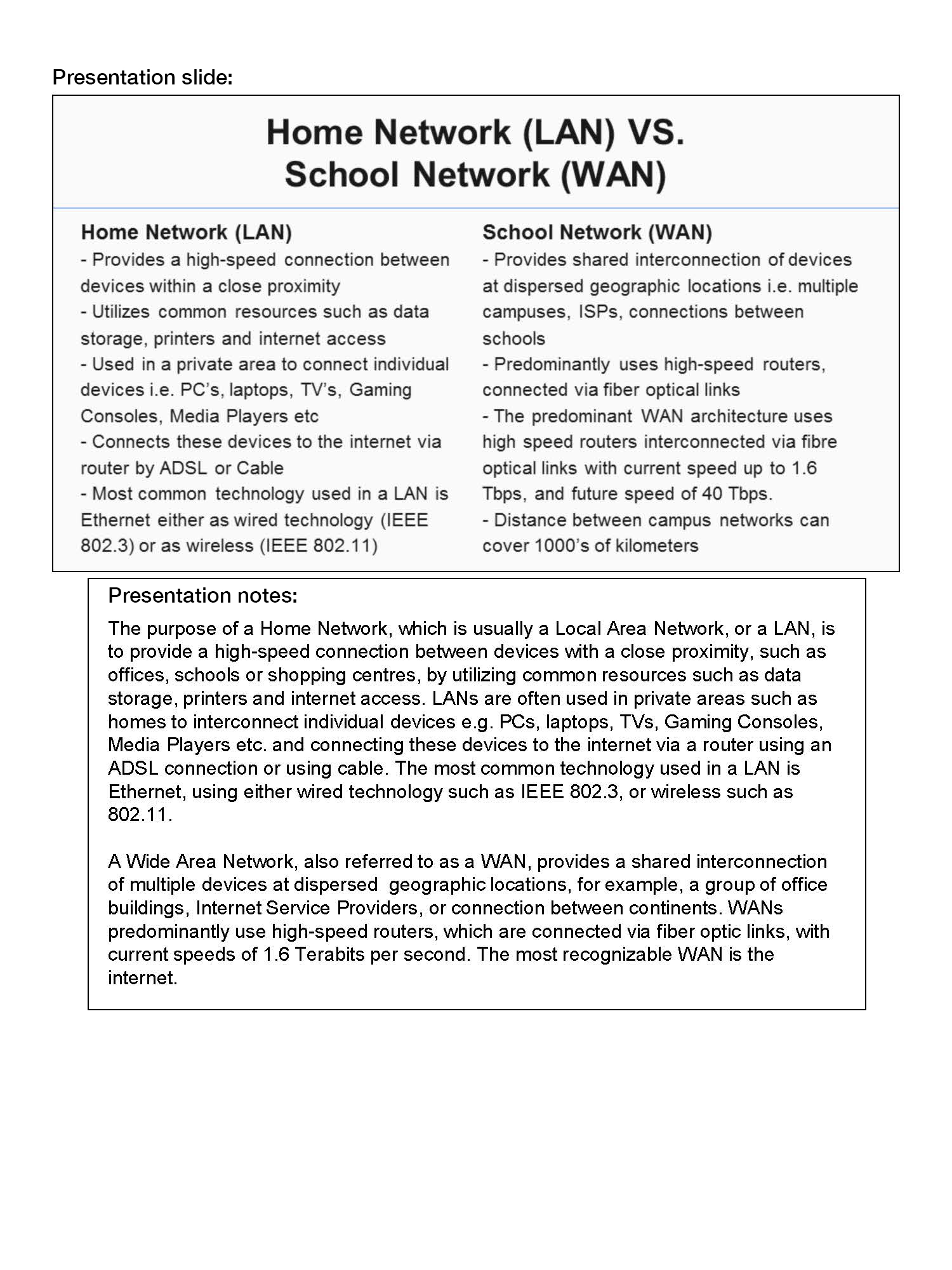
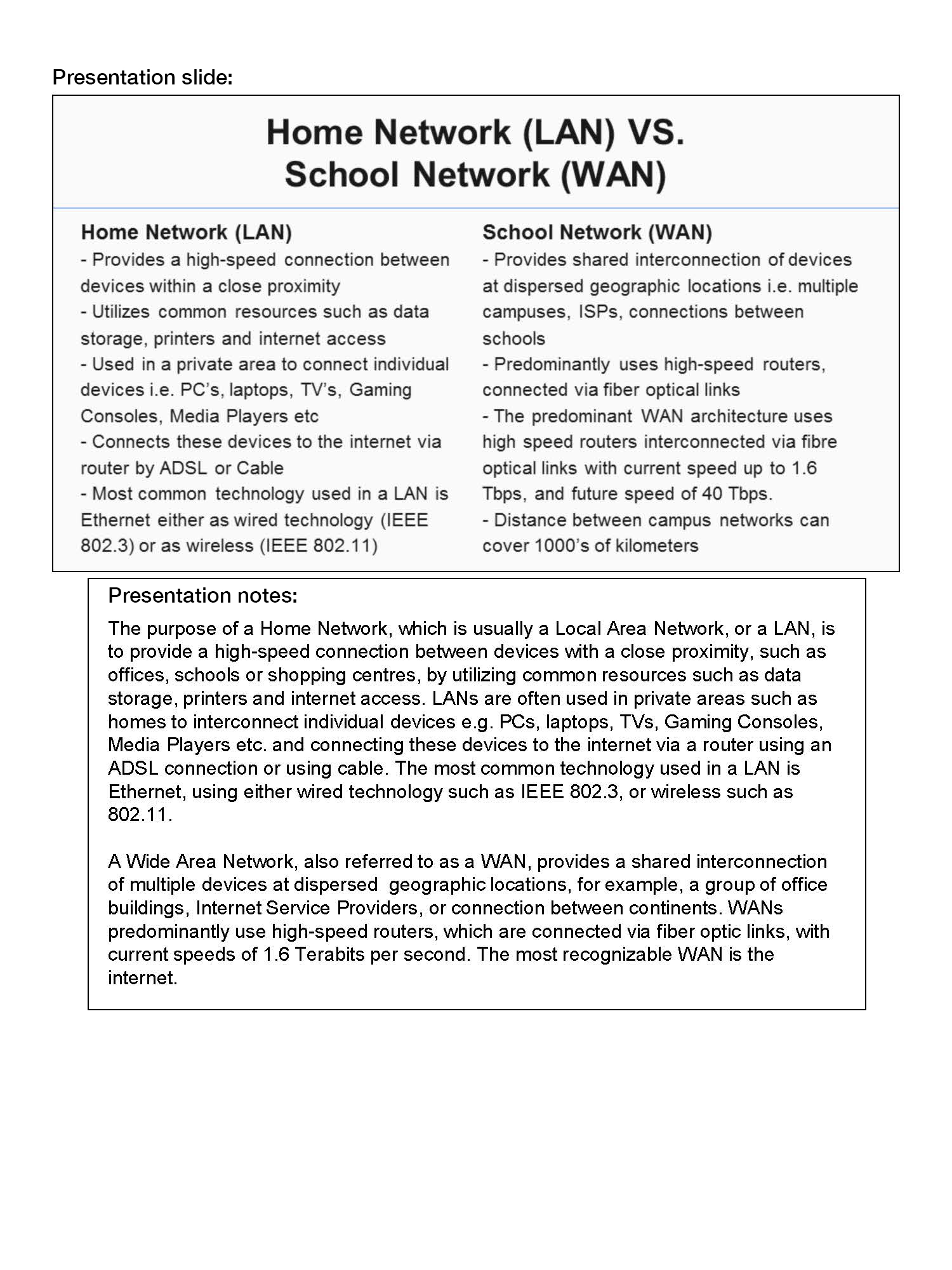
Identifies key differences and similarities between the home local area network (LAN) and the school system wide area network (WAN)
-
Annotations
-
1
Annotation 1
Identifies key differences and similarities between the home local area network (LAN) and the school system wide area network (WAN)
 1
Annotation 1
1
Annotation 1
Provides images to illustrate the difference between a LAN and WAN including the interactions between different hardware components
-
Annotations
-
1
Annotation 1
Provides images to illustrate the difference between a LAN and WAN including the interactions between different hardware components
 1
Annotation 1
1
Annotation 1
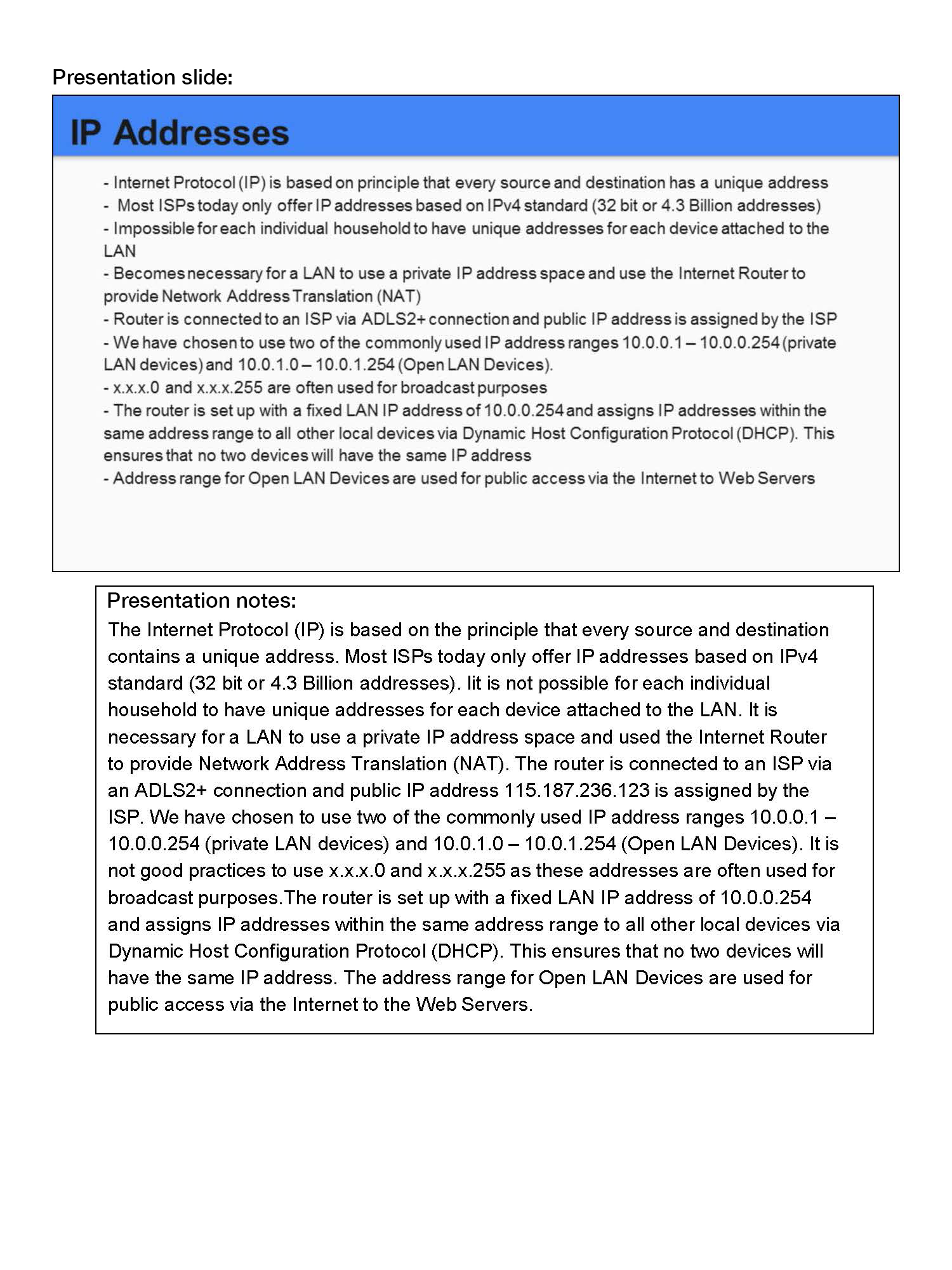
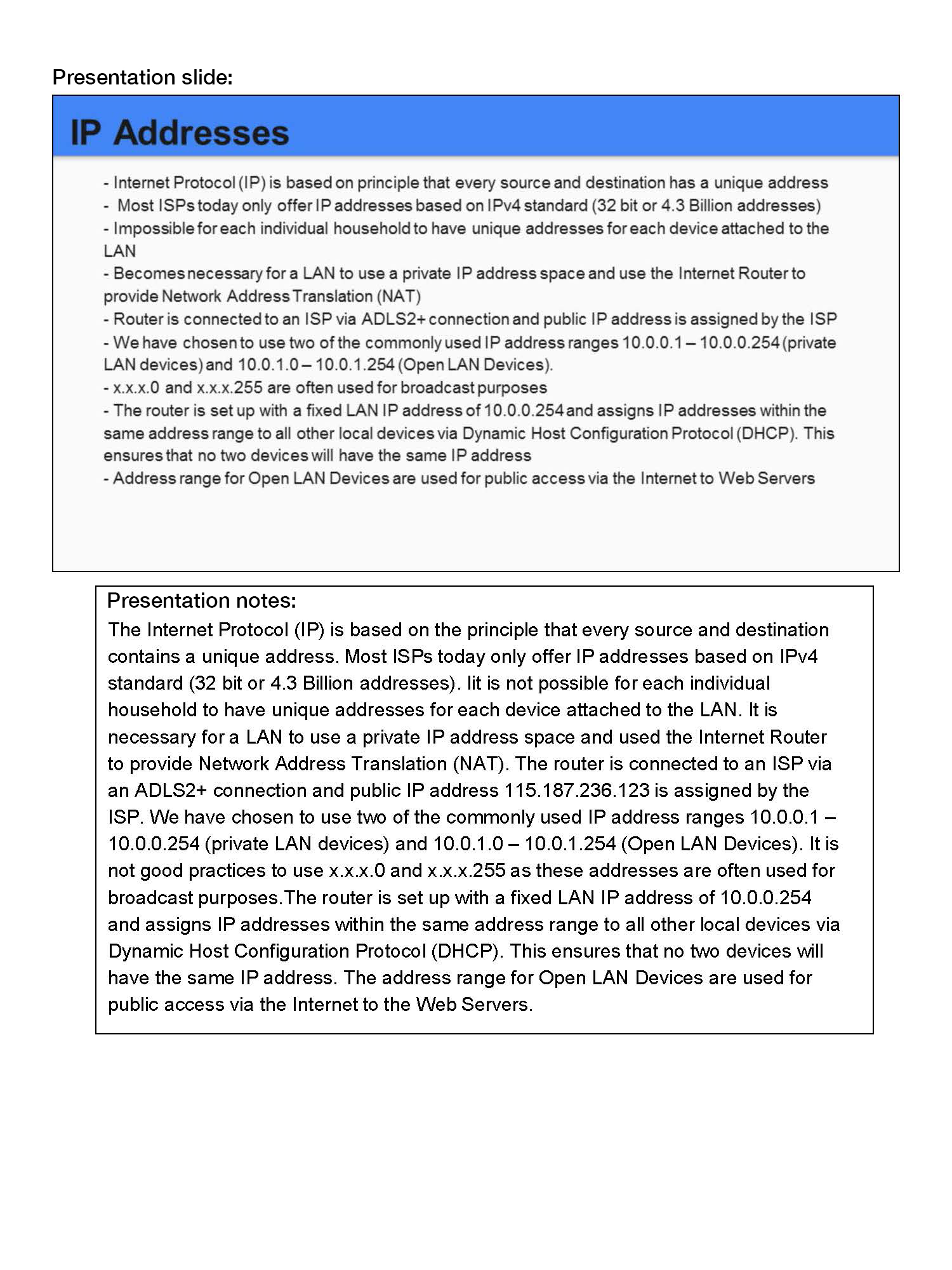
Explains the need for internal management and control hardware, that is, private addressing, and how it allocates addresses
-
Annotations
-
1
Annotation 1
Explains the need for internal management and control hardware, that is, private addressing, and how it allocates addresses
 1
Annotation 1
1
Annotation 1
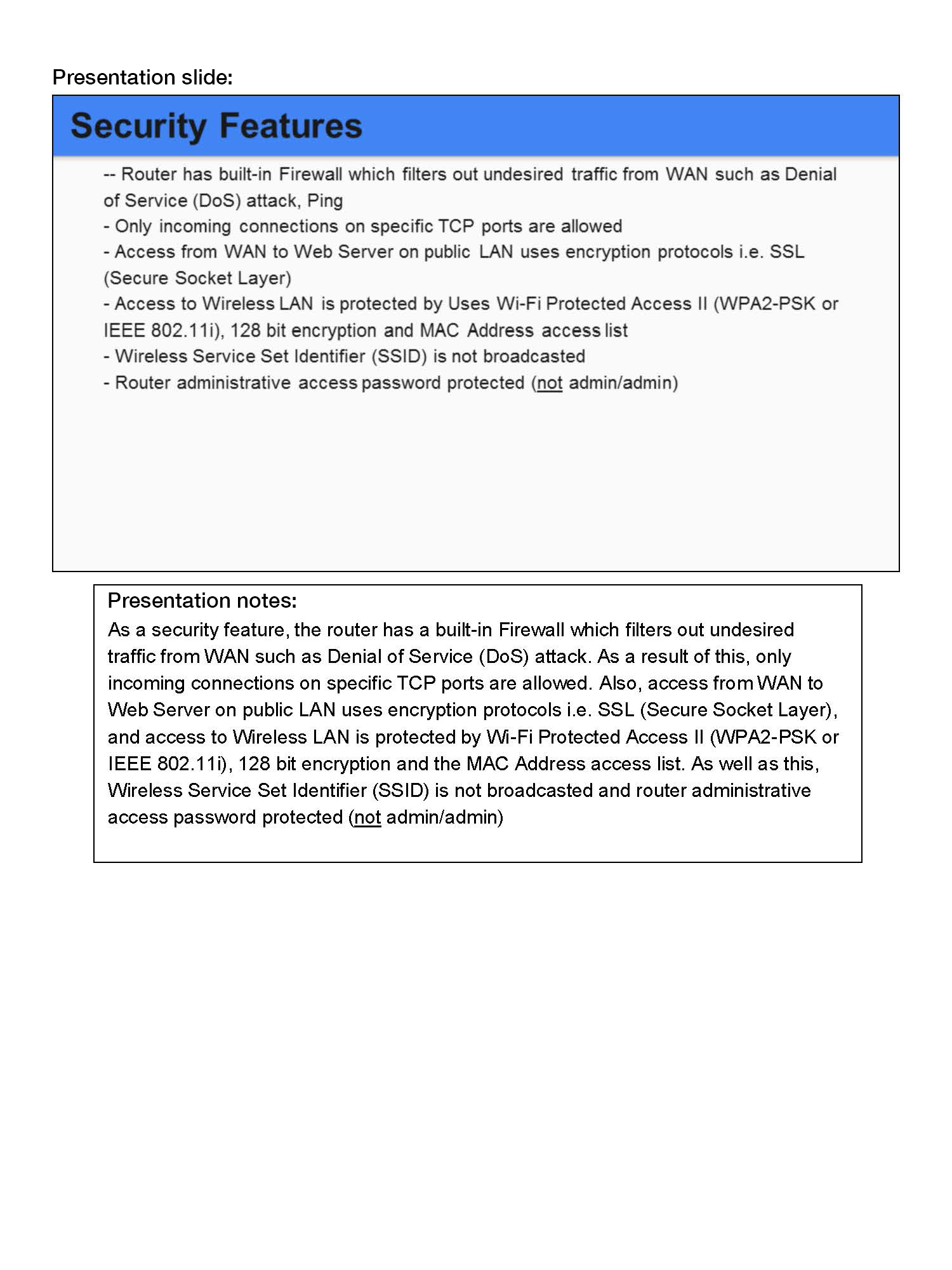
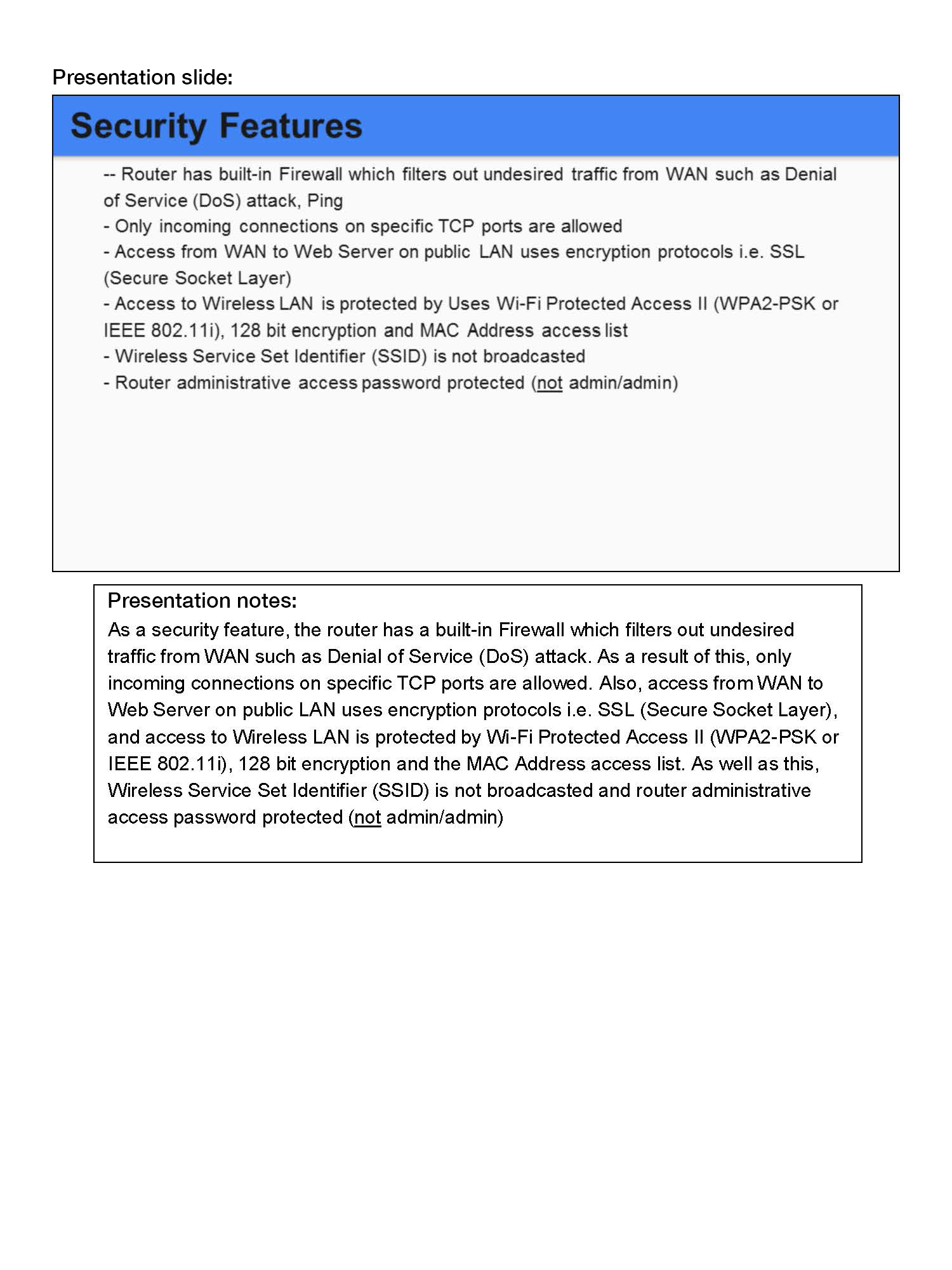
Identifies a range of security mechanisms and the risks they mitigate
-
Annotations
-
1
Annotation 1
Identifies a range of security mechanisms and the risks they mitigate
 1
Annotation 1
1
Annotation 1
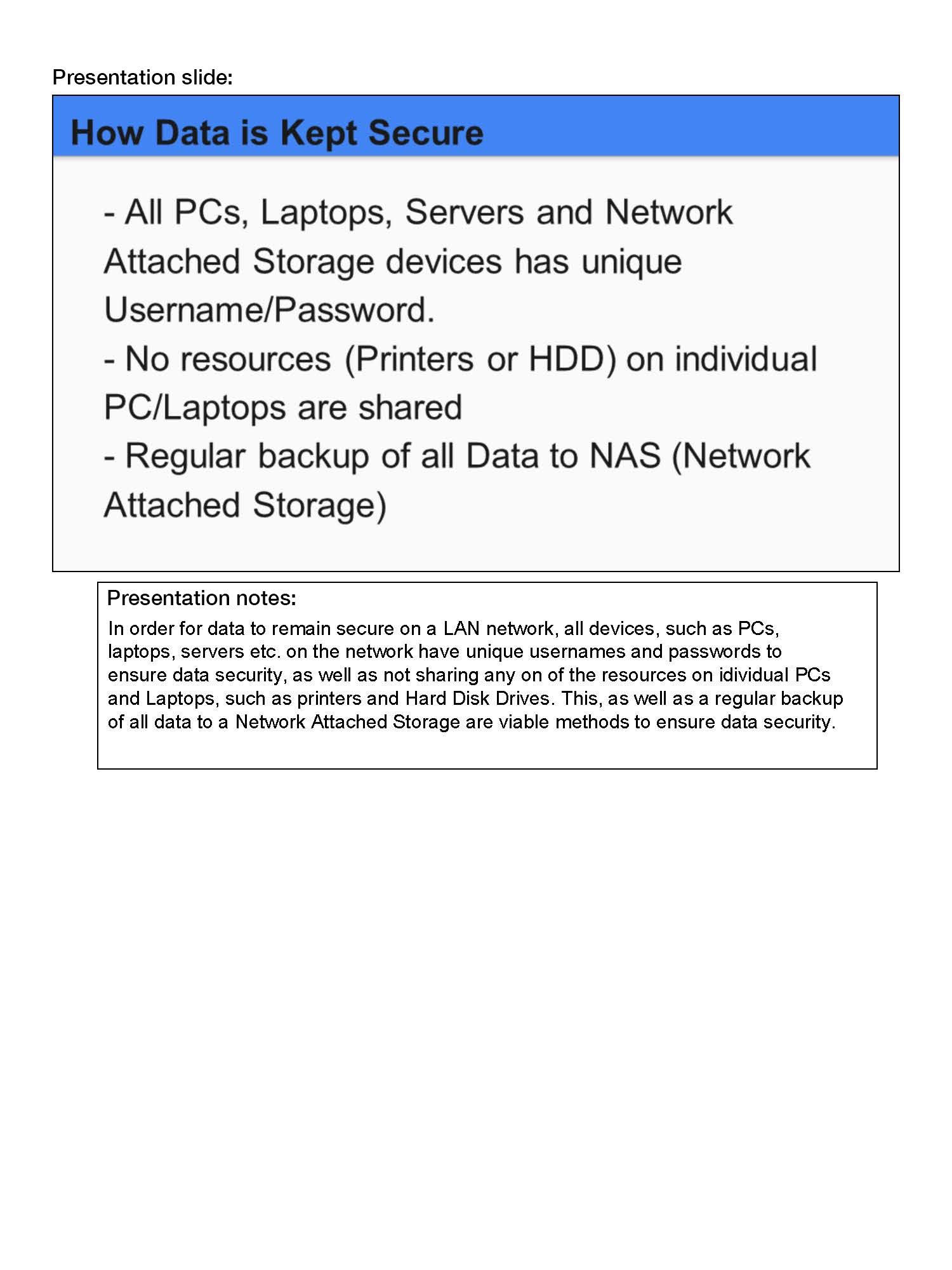
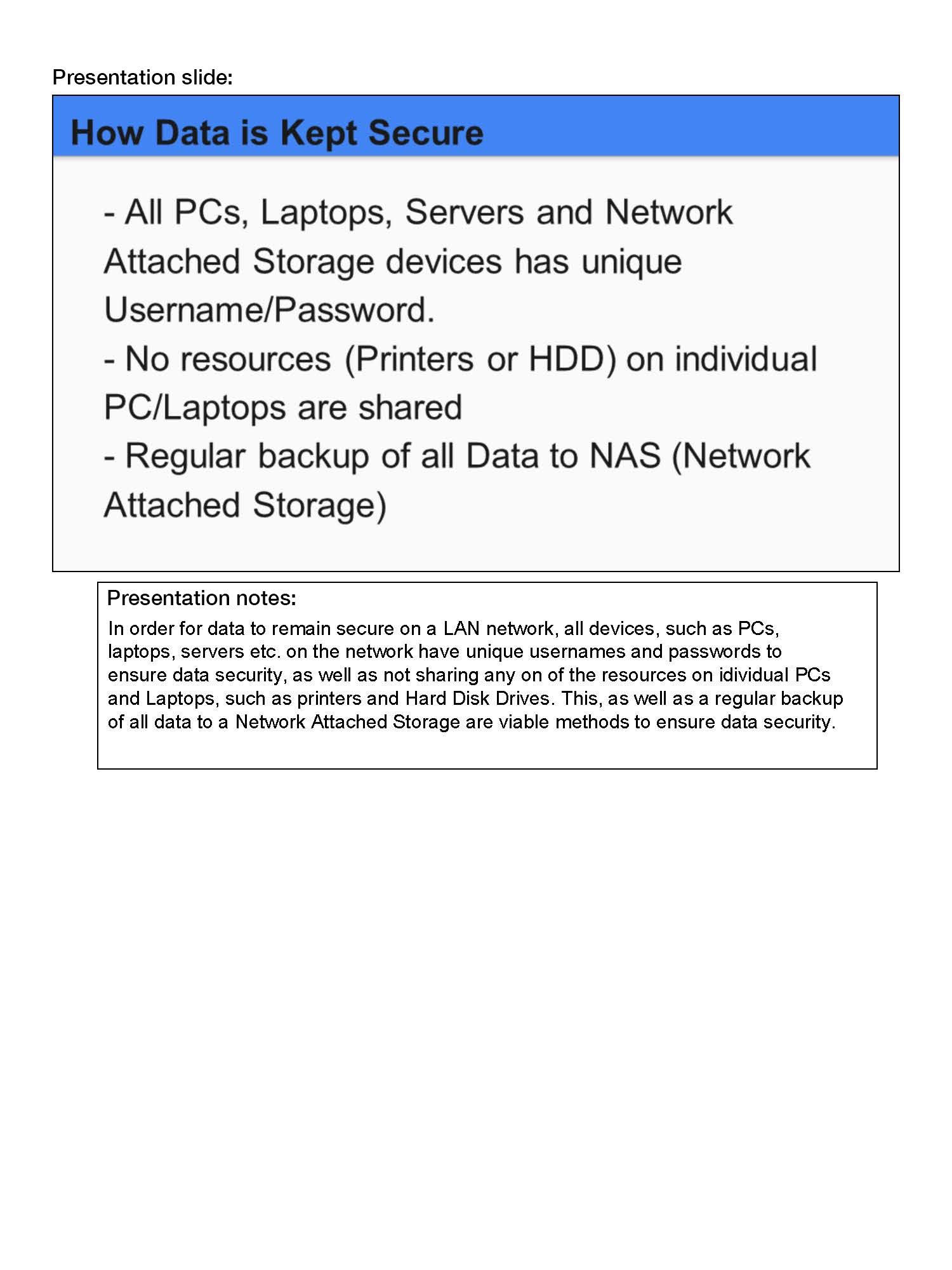
Identifies how data are kept secure on the school network
-
Annotations
-
1
Annotation 1
Identifies how data are kept secure on the school network
 1
Annotation 1
1
Annotation 1
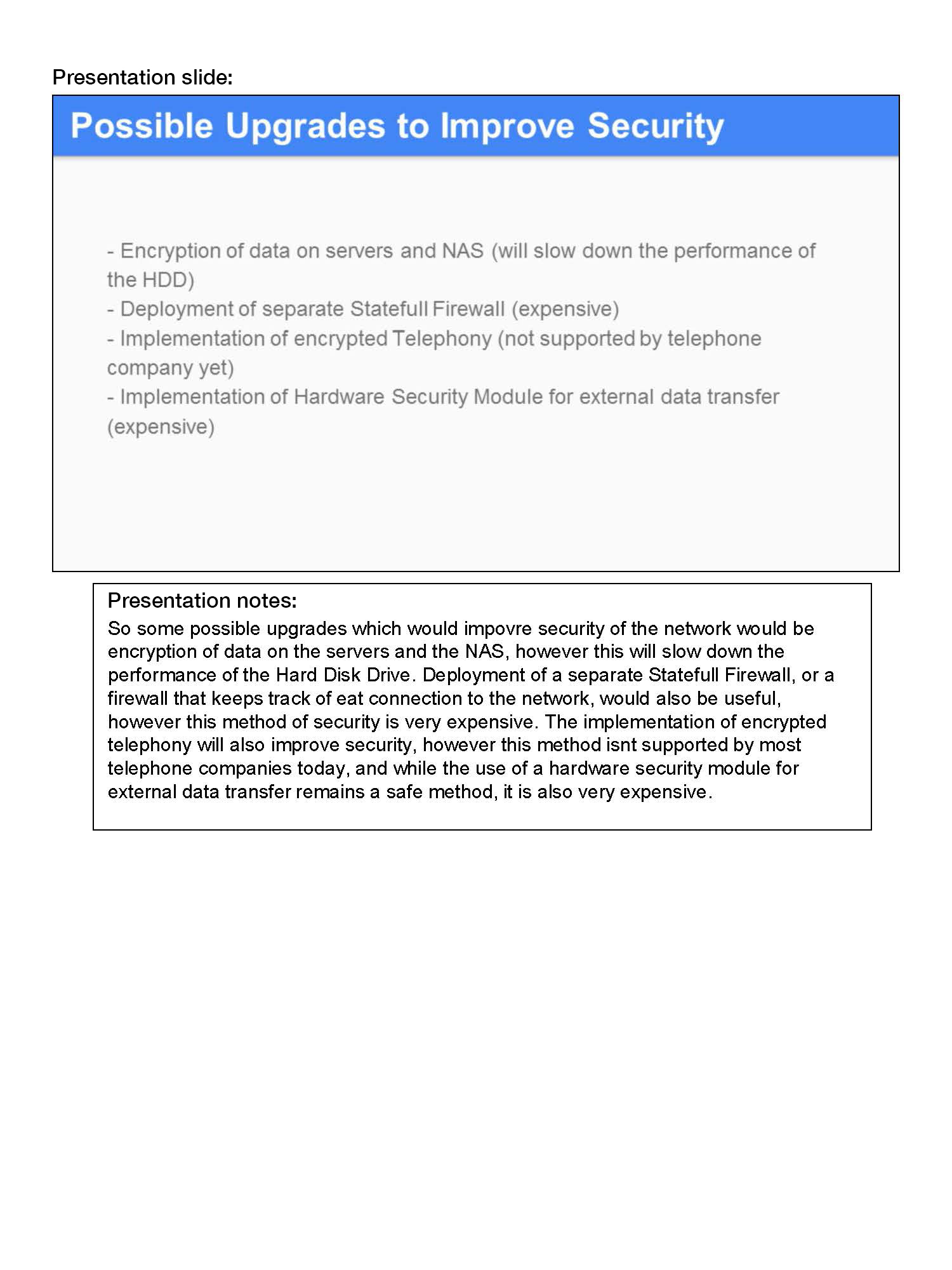
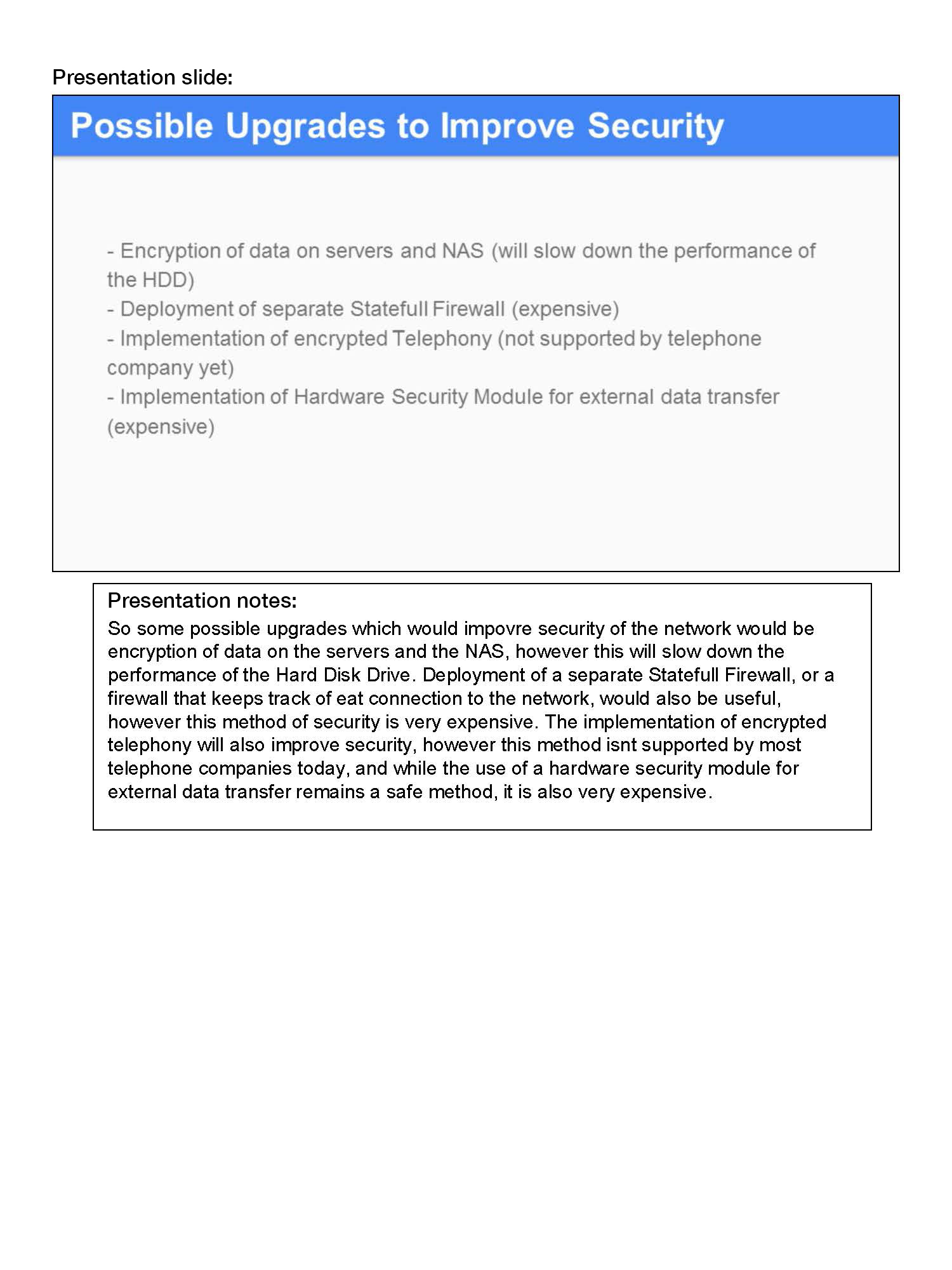
Demonstrates understanding of the concept of the appropriateness of security for a situation, by suggesting how to improve security and identifying the implications of each suggestion
-
Annotations
-
1
Annotation 1
Demonstrates understanding of the concept of the appropriateness of security for a situation, by suggesting how to improve security and identifying the implications of each suggestion
 1
Annotation 1
1
Annotation 1
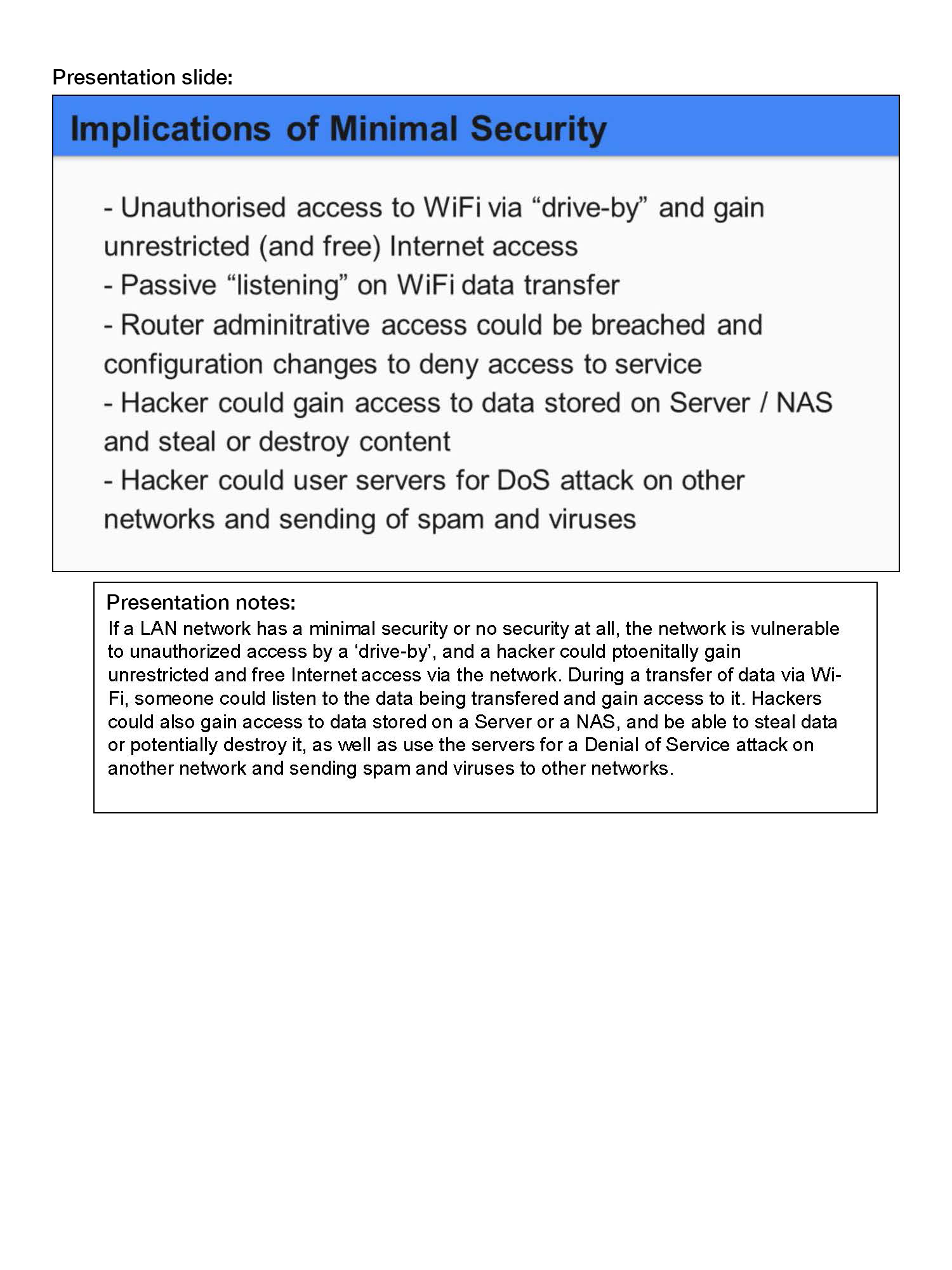
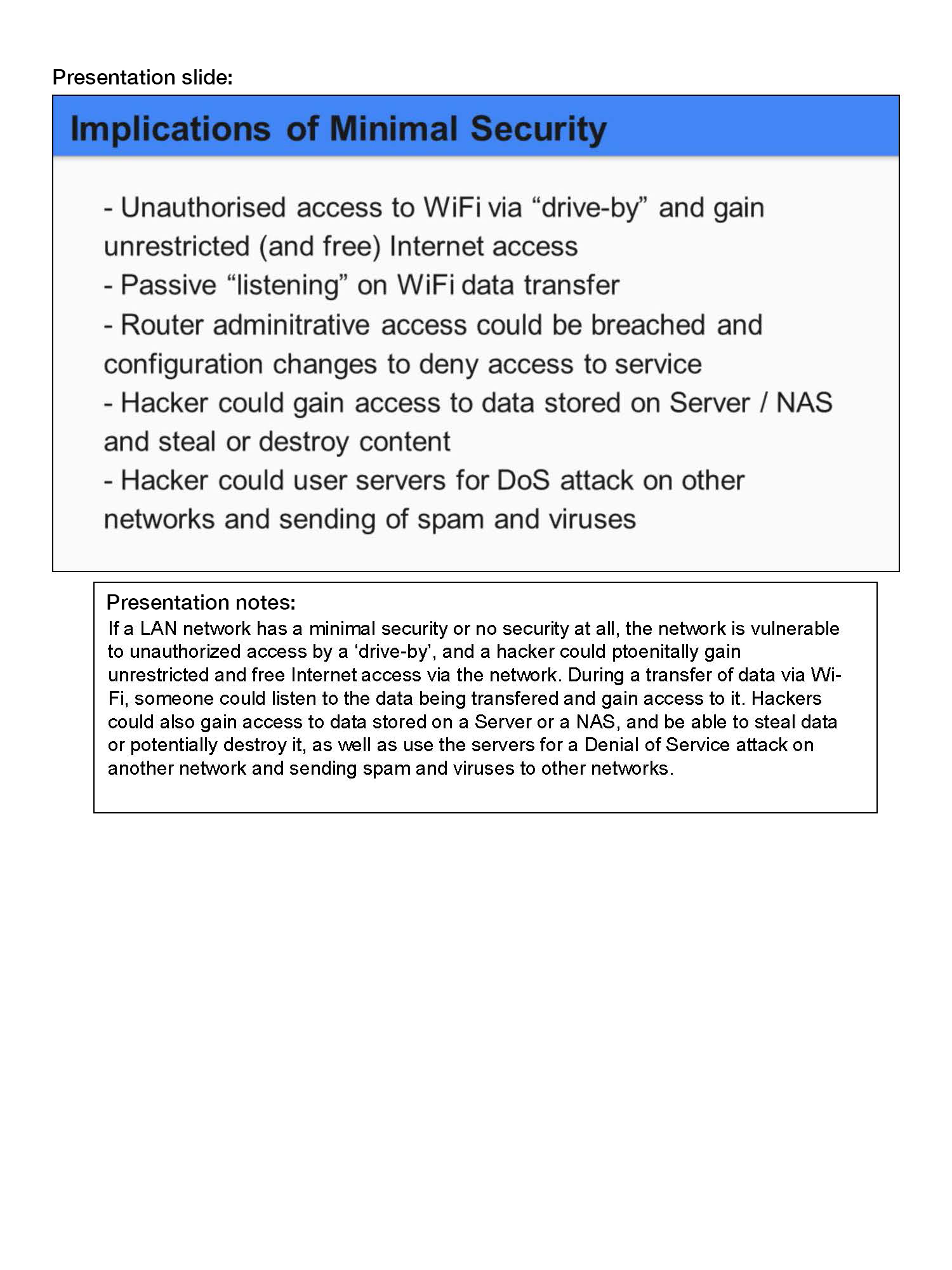
Explains a range of implications of not taking appropriate security precautions
-
Annotations
-
1
Annotation 1
Explains a range of implications of not taking appropriate security precautions
 1
Annotation 1
1
Annotation 1
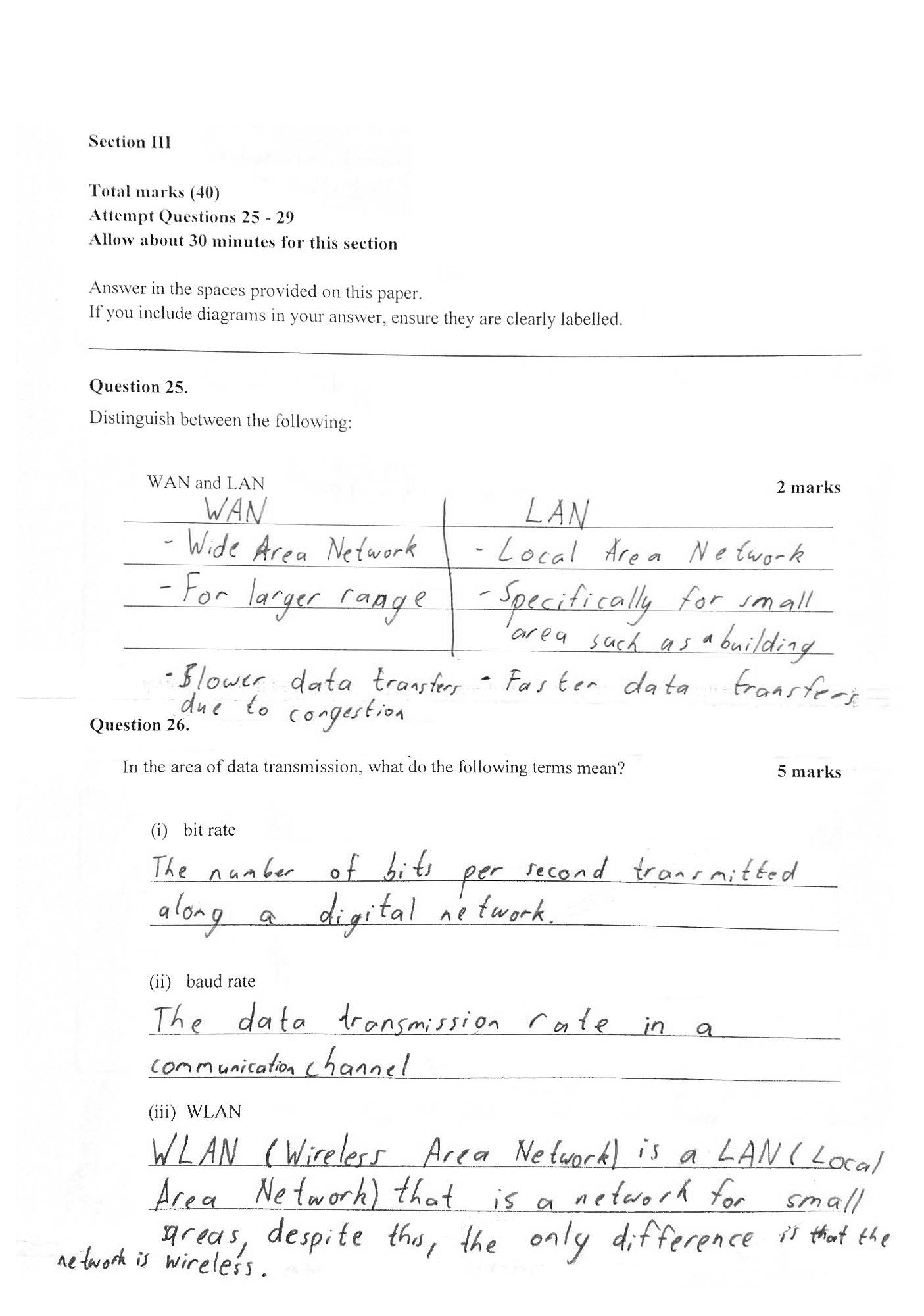
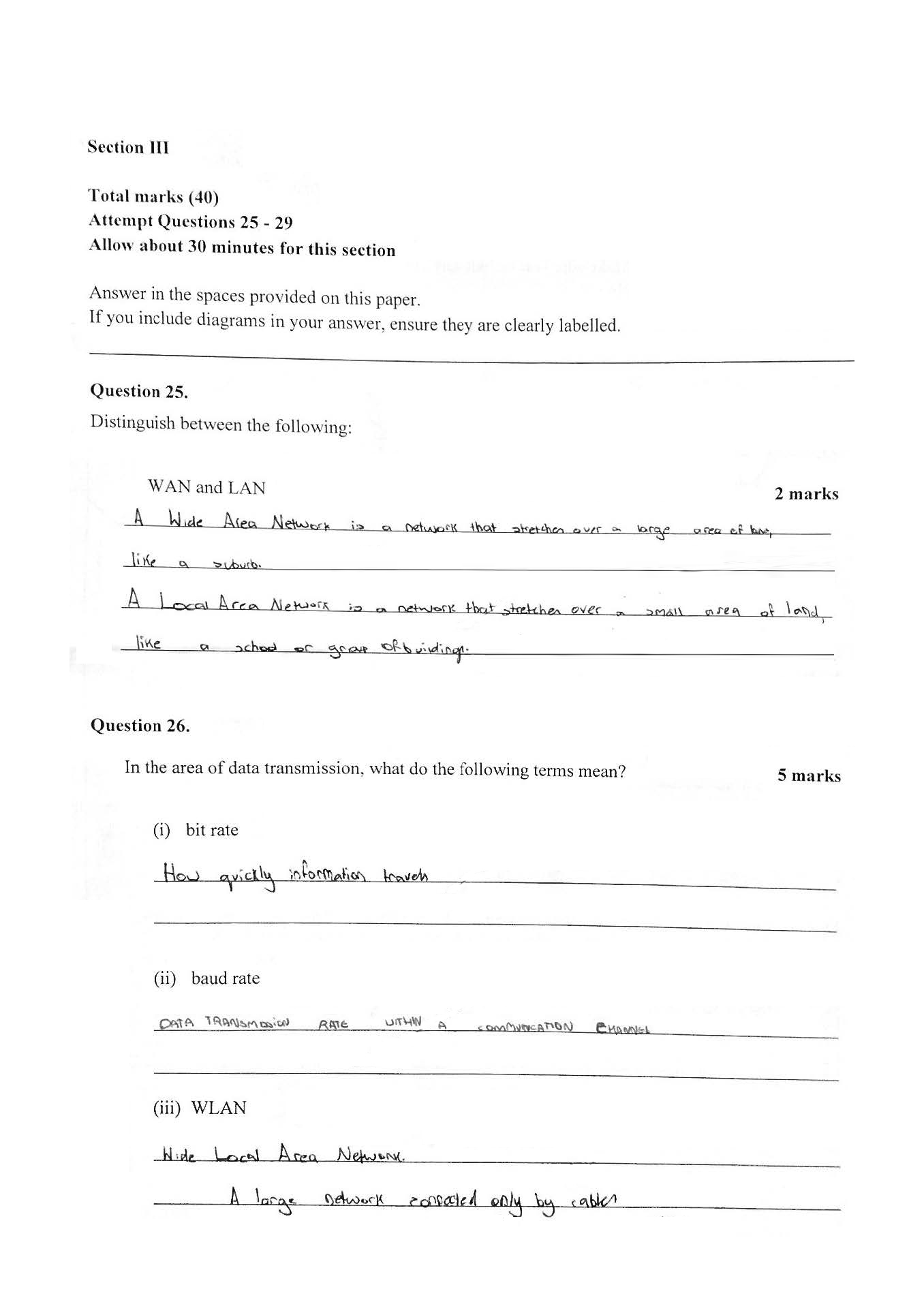
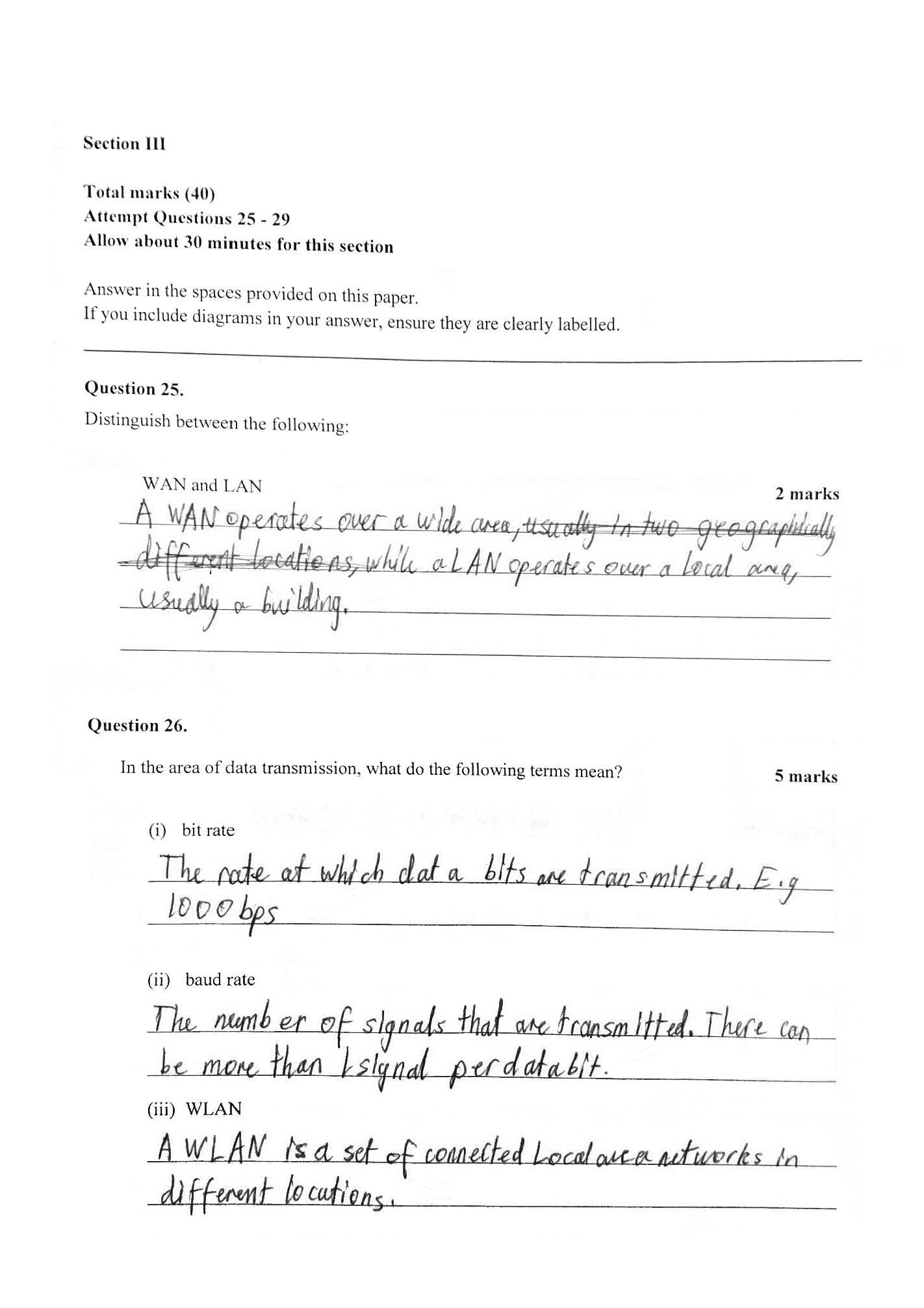
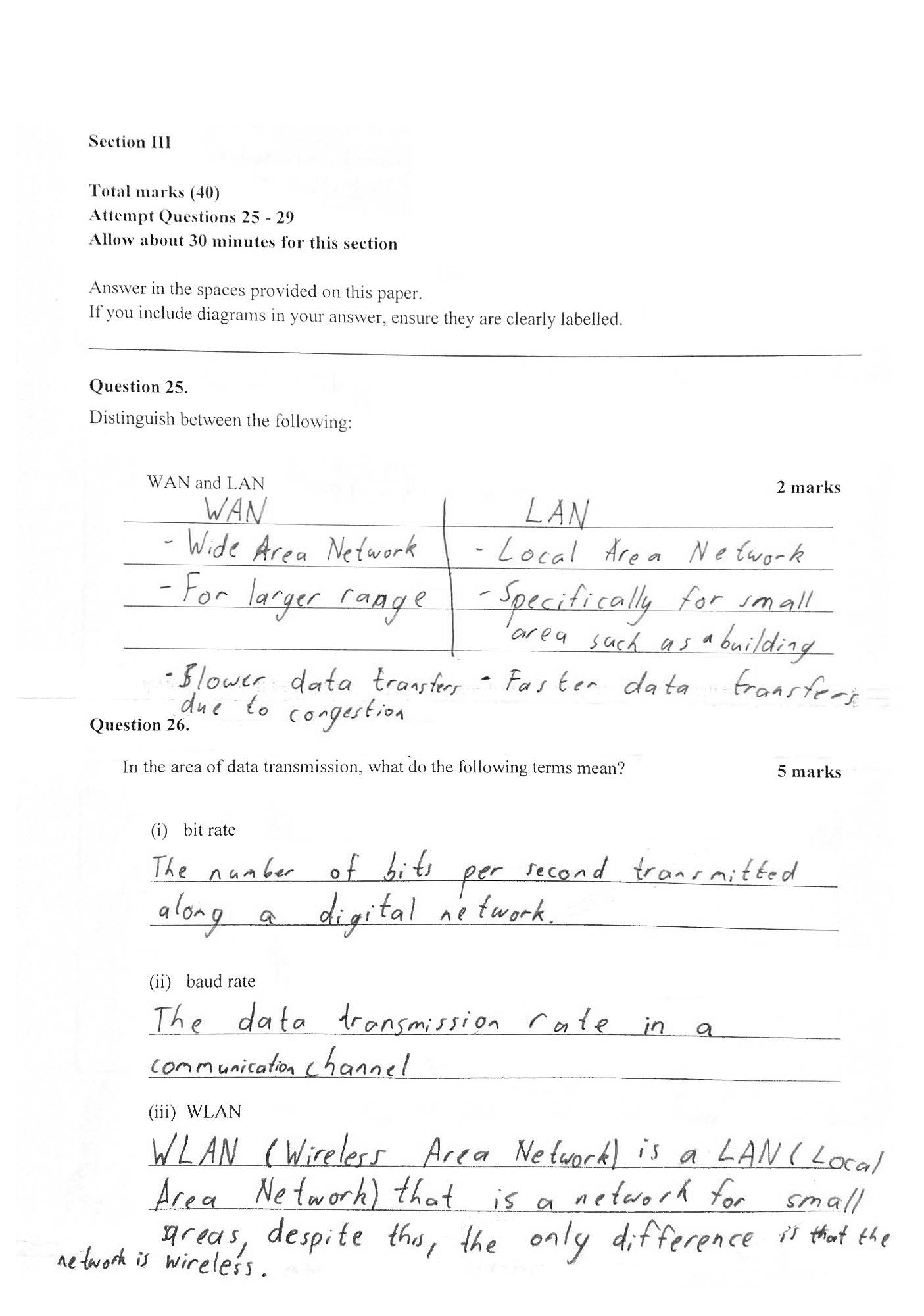
Demonstrates knowledge of correct terminology related to data transmission
-
Annotations
-
1
Annotation 1
Demonstrates knowledge of correct terminology related to data transmission
 1
Annotation 1
1
Annotation 1
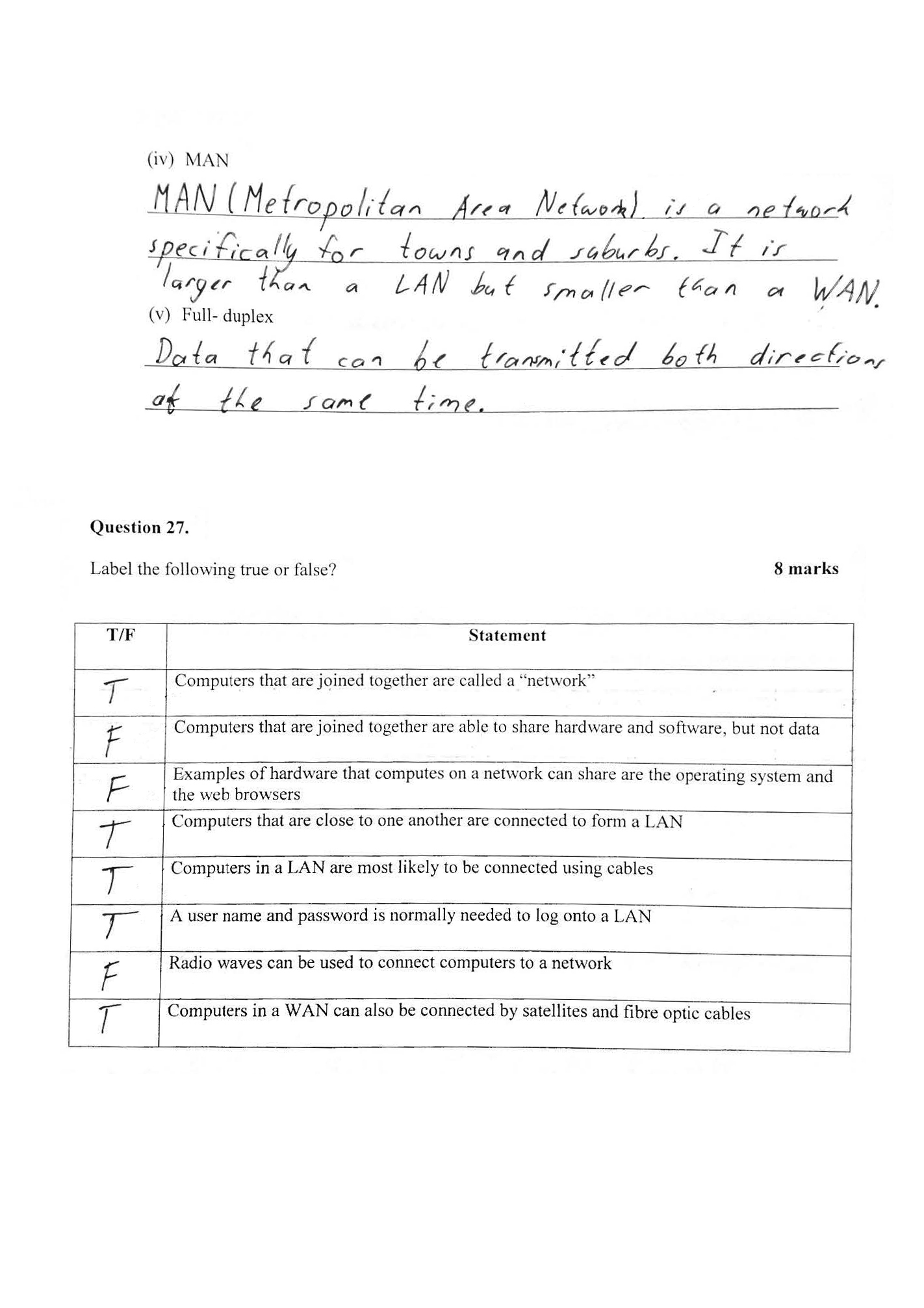
Demonstrates sound understanding of the interactions between hardware, software and users
-
Annotations
-
1
Annotation 1
Demonstrates sound understanding of the interactions between hardware, software and users
 1
Annotation 1
1
Annotation 1
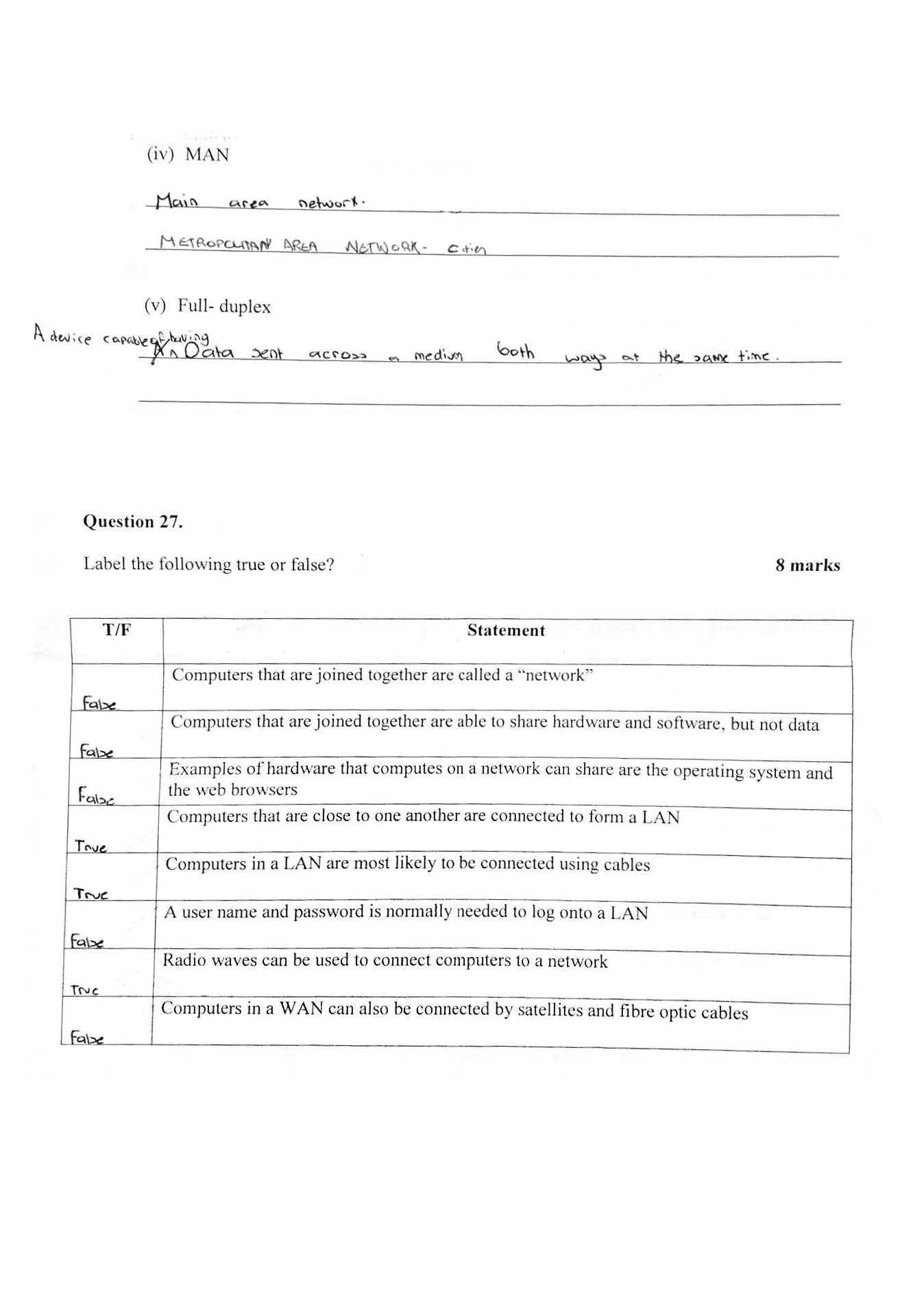
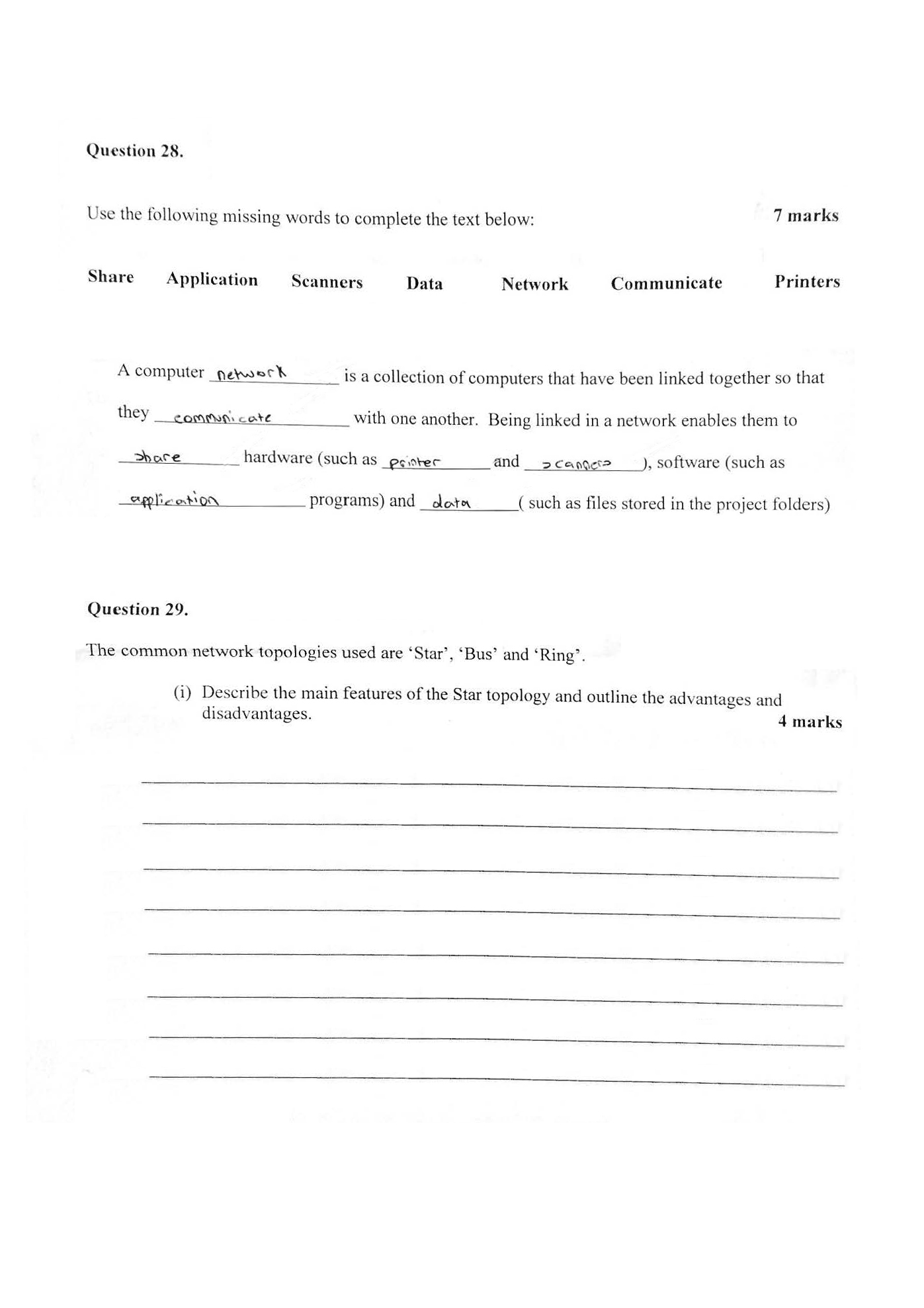
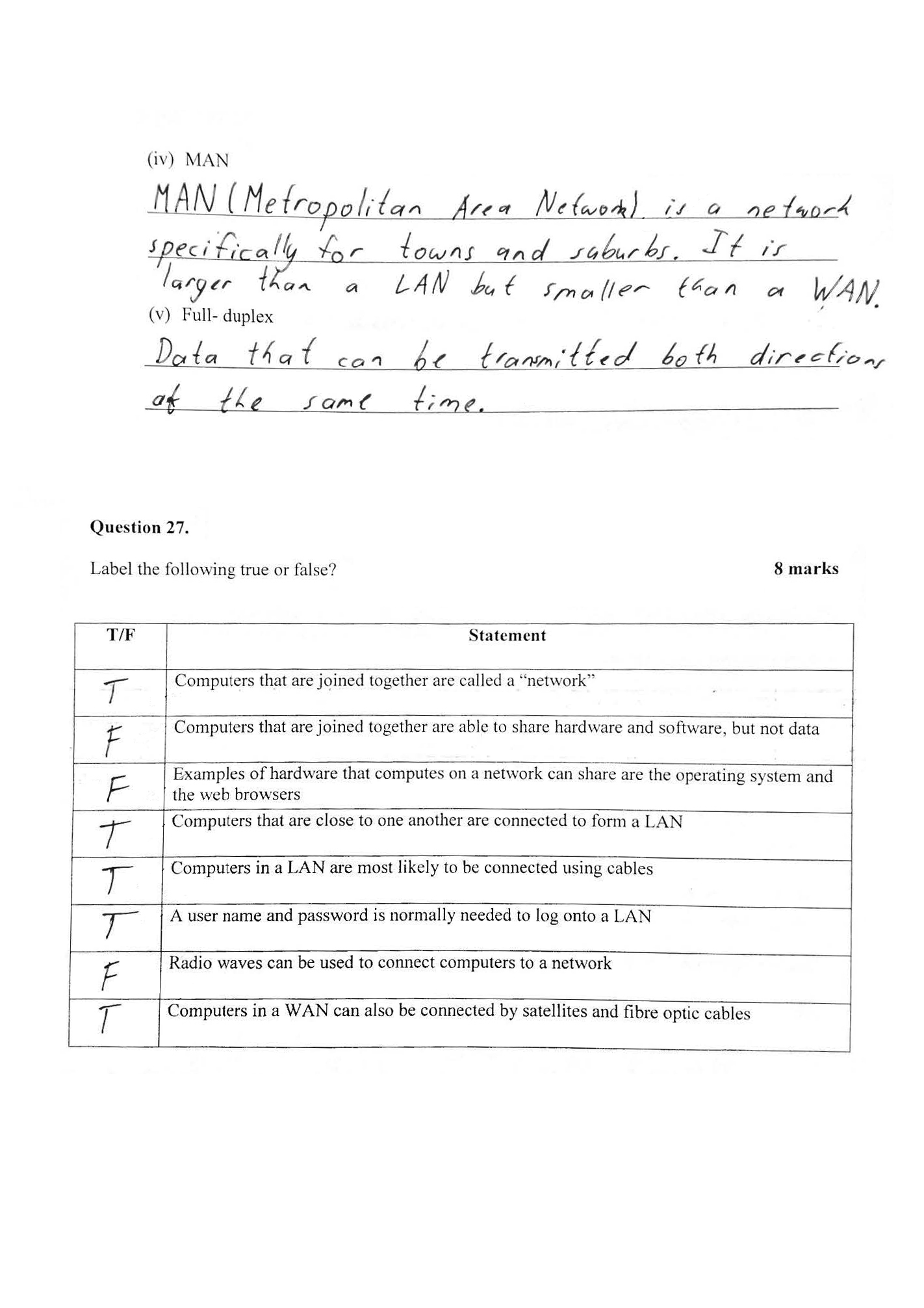
Identifies correctly how hardware is linked together on a network 2 Annotation 2
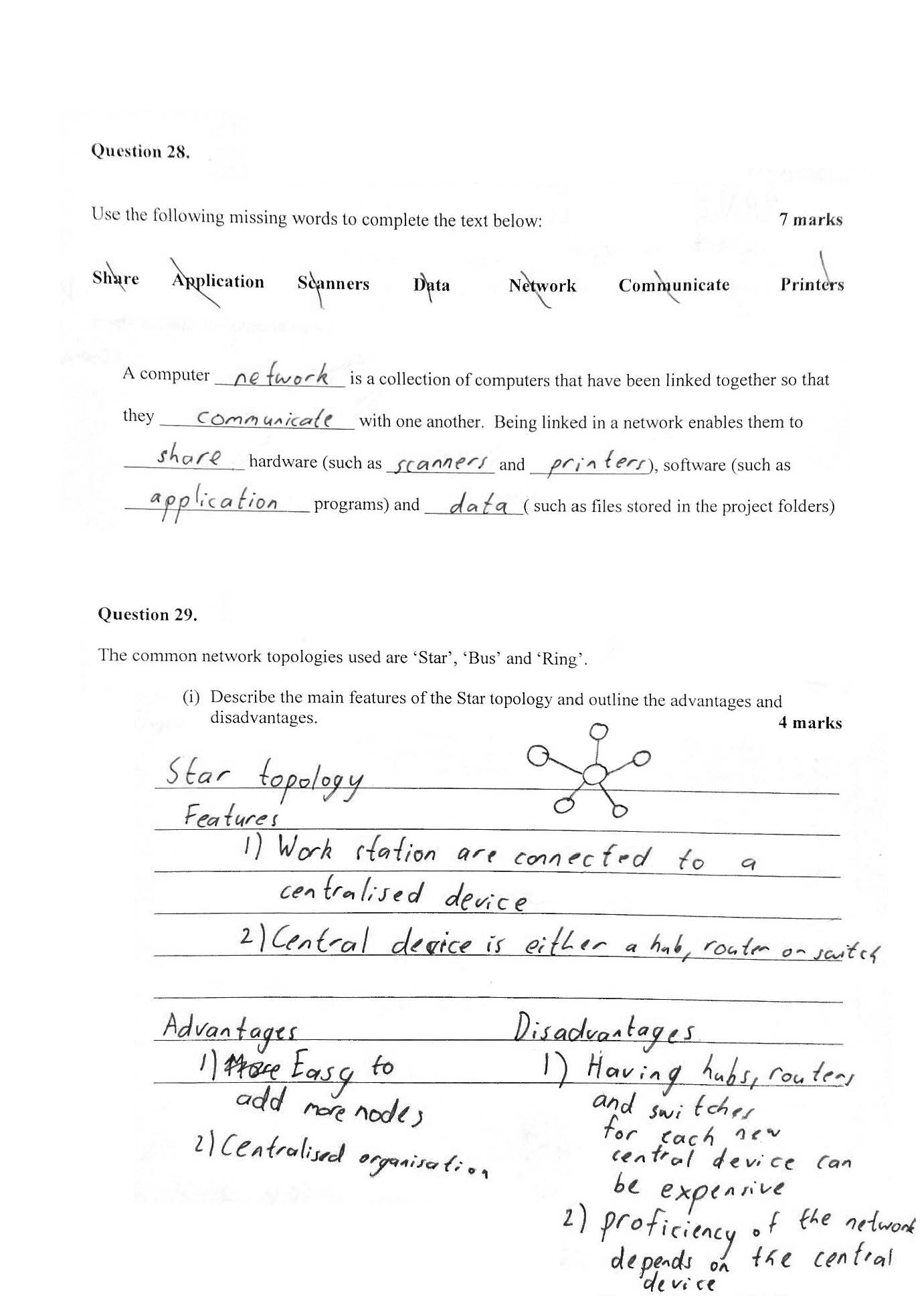
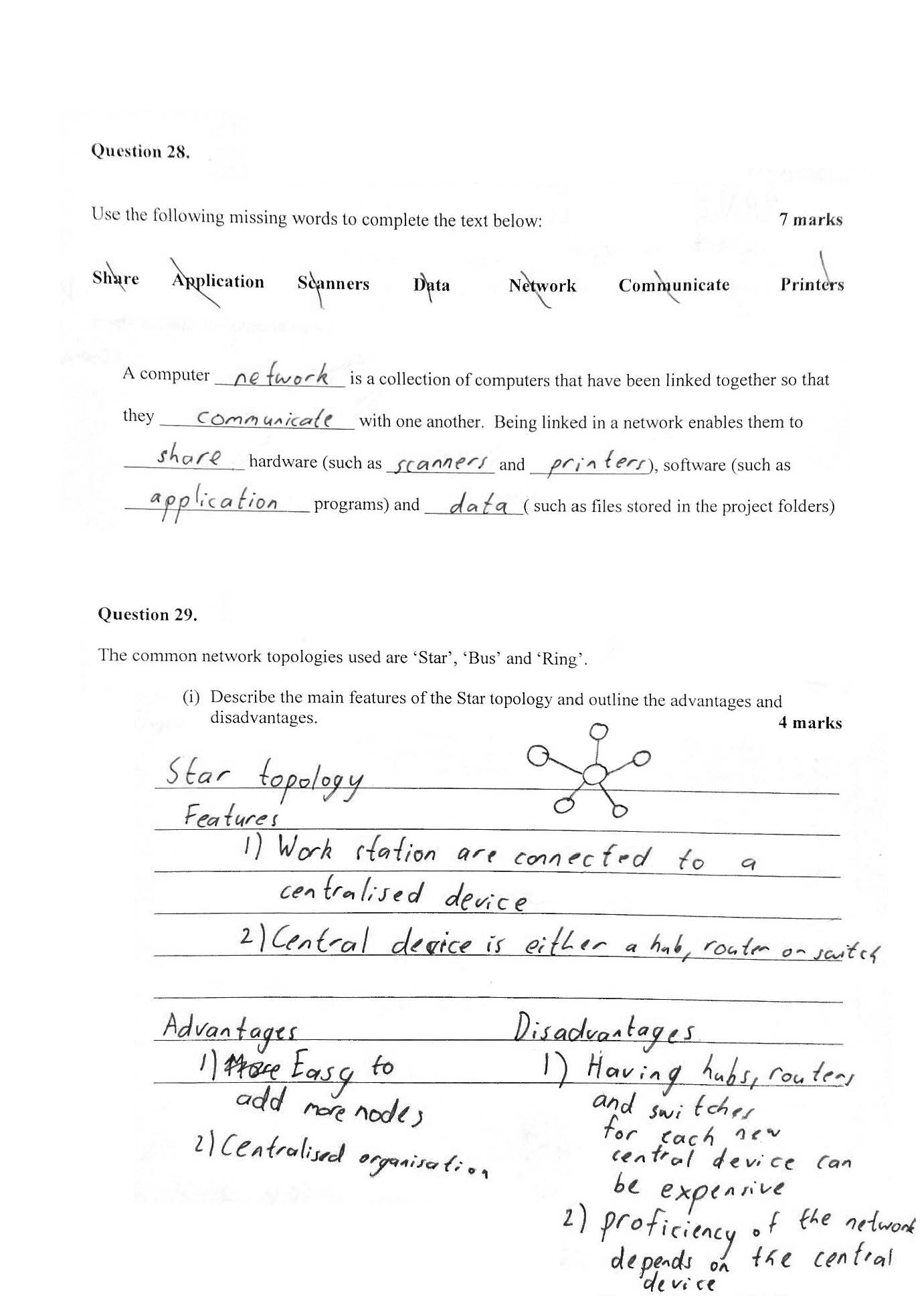
Summarises succinctly the main features of a star topology and identifies pertinent advantages and disadvantages
-
Annotations
-
1
Annotation 1
Identifies correctly how hardware is linked together on a network -
2
Annotation 2
Summarises succinctly the main features of a star topology and identifies pertinent advantages and disadvantages
 1
Annotation 1
1
Annotation 1
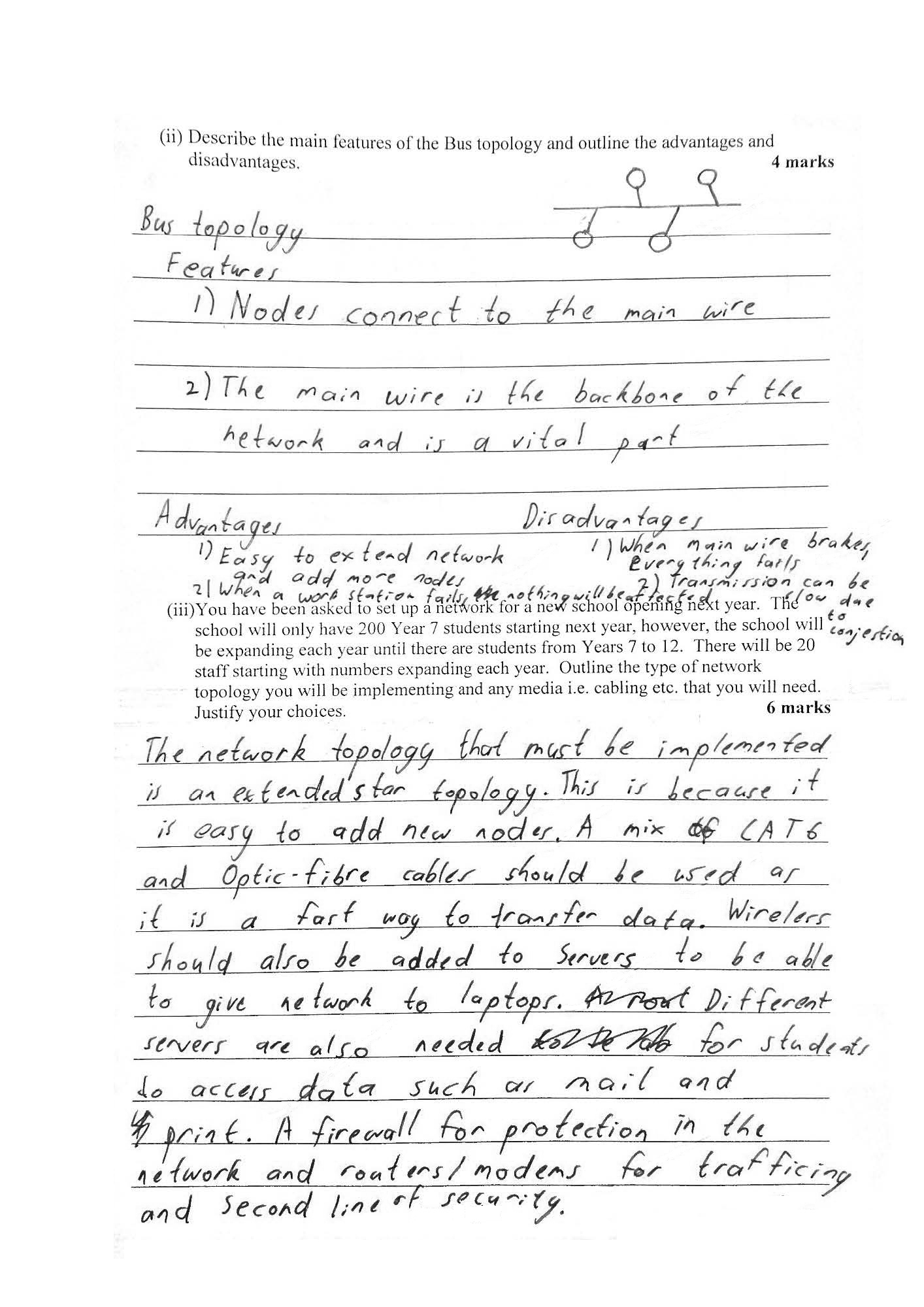
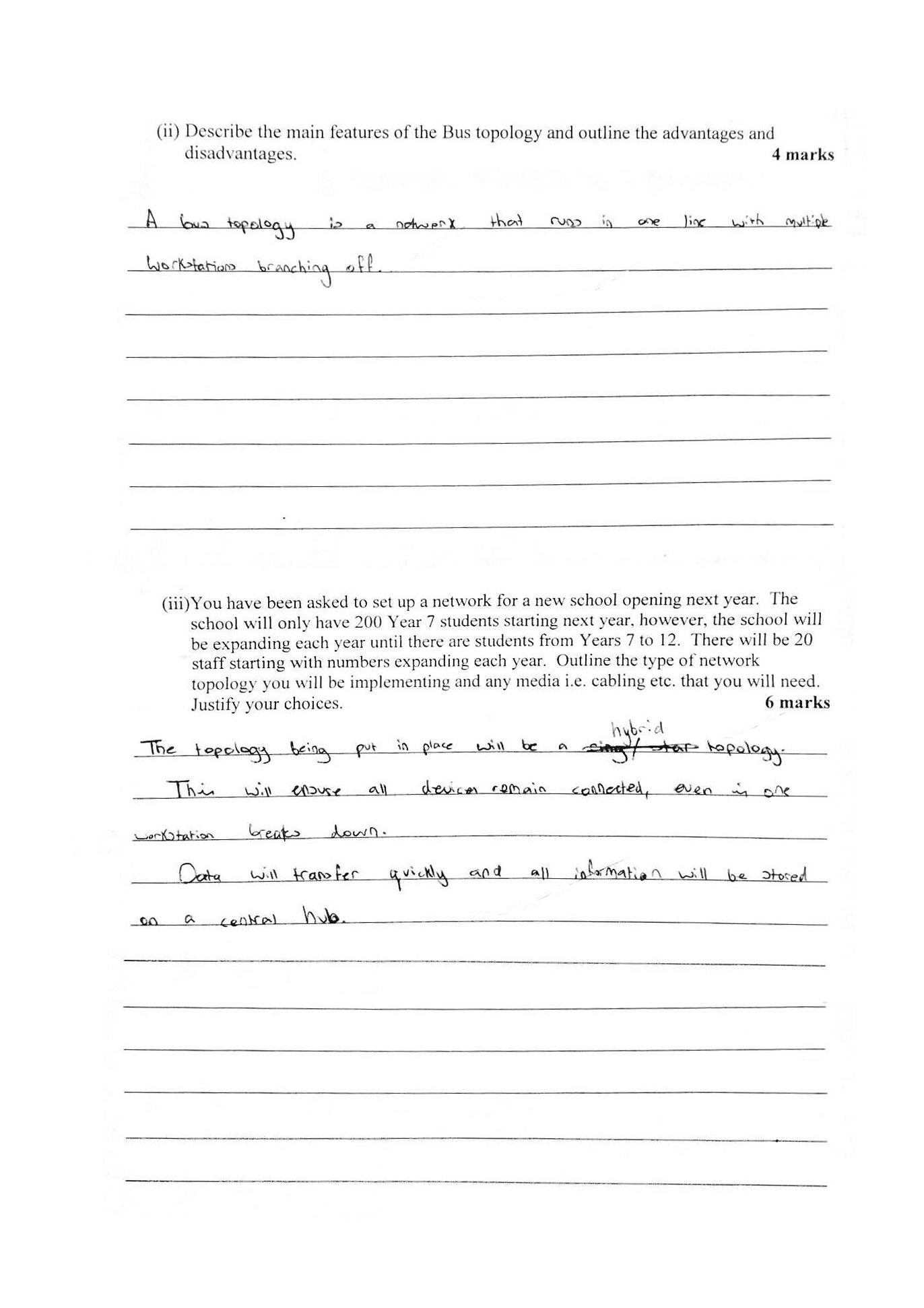
Summarises succinctly the main features of a bus topology and identifies pertinent advantages and disadvantages 2 Annotation 2
Selects and explains appropriate topology including the mix of technologies required that balance both purpose and performance, and allow for growth
-
Annotations
-
1
Annotation 1
Summarises succinctly the main features of a bus topology and identifies pertinent advantages and disadvantages -
2
Annotation 2
Selects and explains appropriate topology including the mix of technologies required that balance both purpose and performance, and allow for growth
 1
Annotation 1
1
Annotation 1
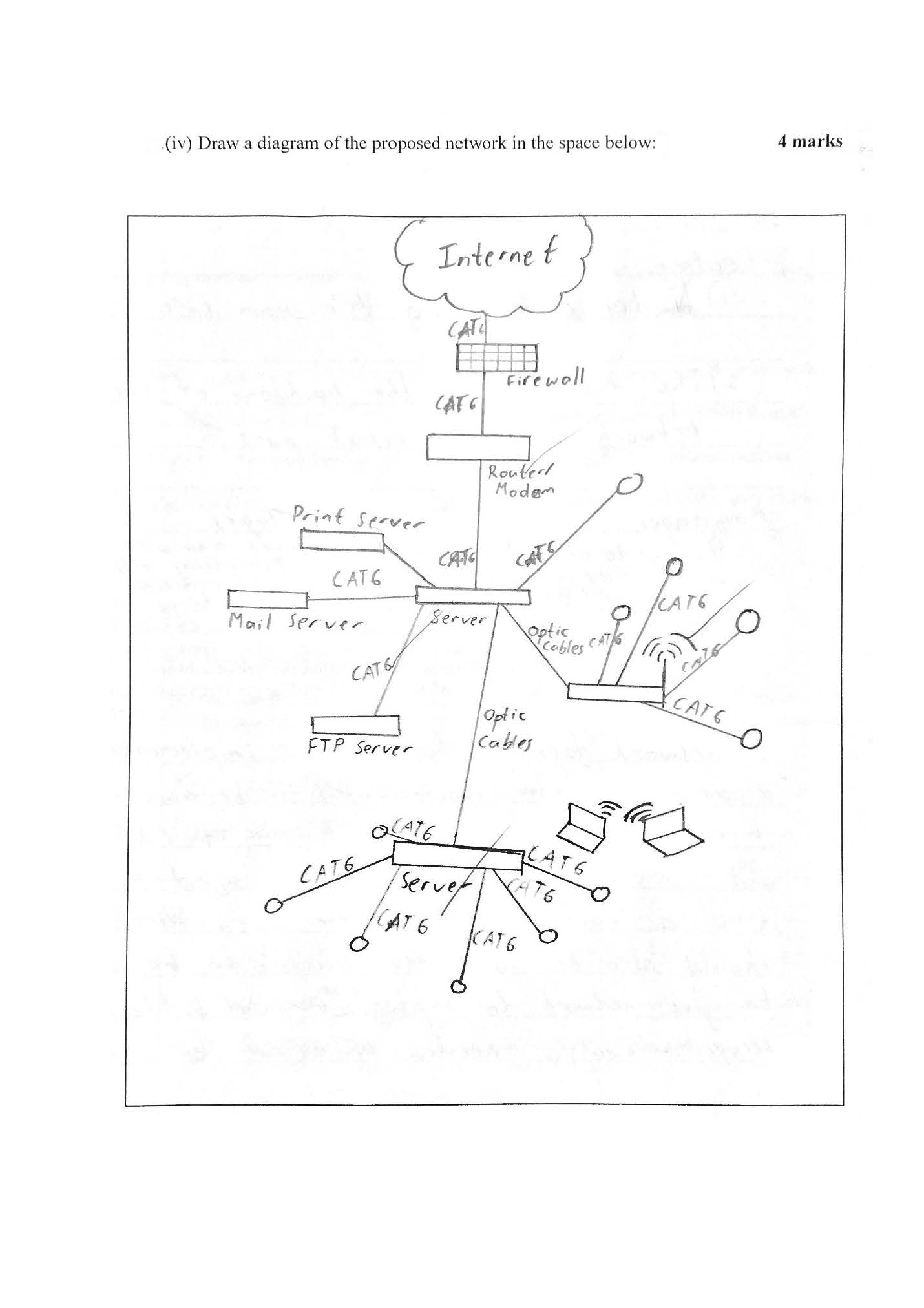
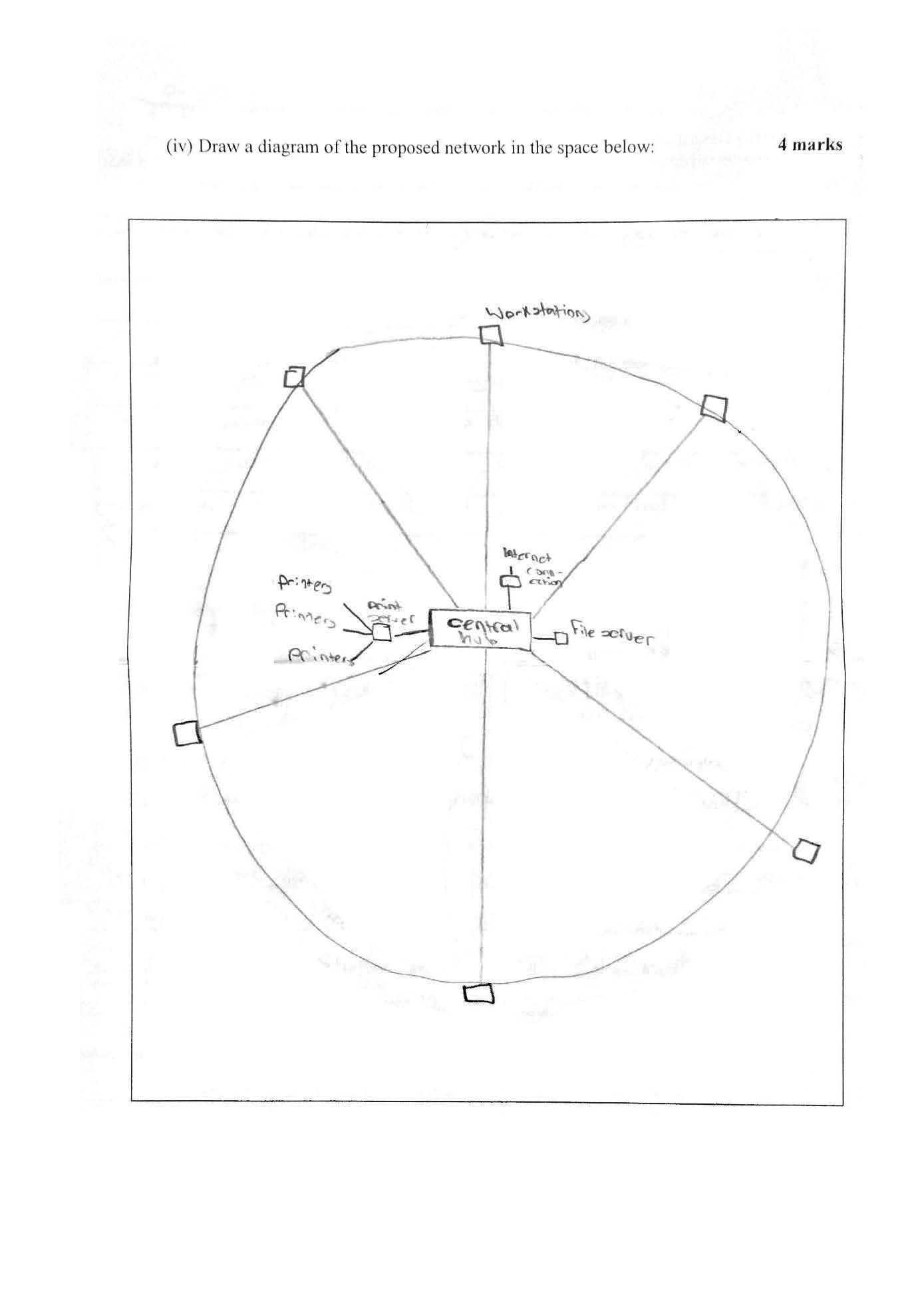
Draws a diagram of an extended star network including a range of connections and using appropriate conventions
-
Annotations
-
1
Annotation 1
Draws a diagram of an extended star network including a range of connections and using appropriate conventions
Below satisfactory
Investigation: Secure networks
 1
Annotation 1
1
Annotation 1
Identifies general purpose of a home network and lists hardware components
-
Annotations
-
1
Annotation 1
Identifies general purpose of a home network and lists hardware components
 1
Annotation 1
1
Annotation 1
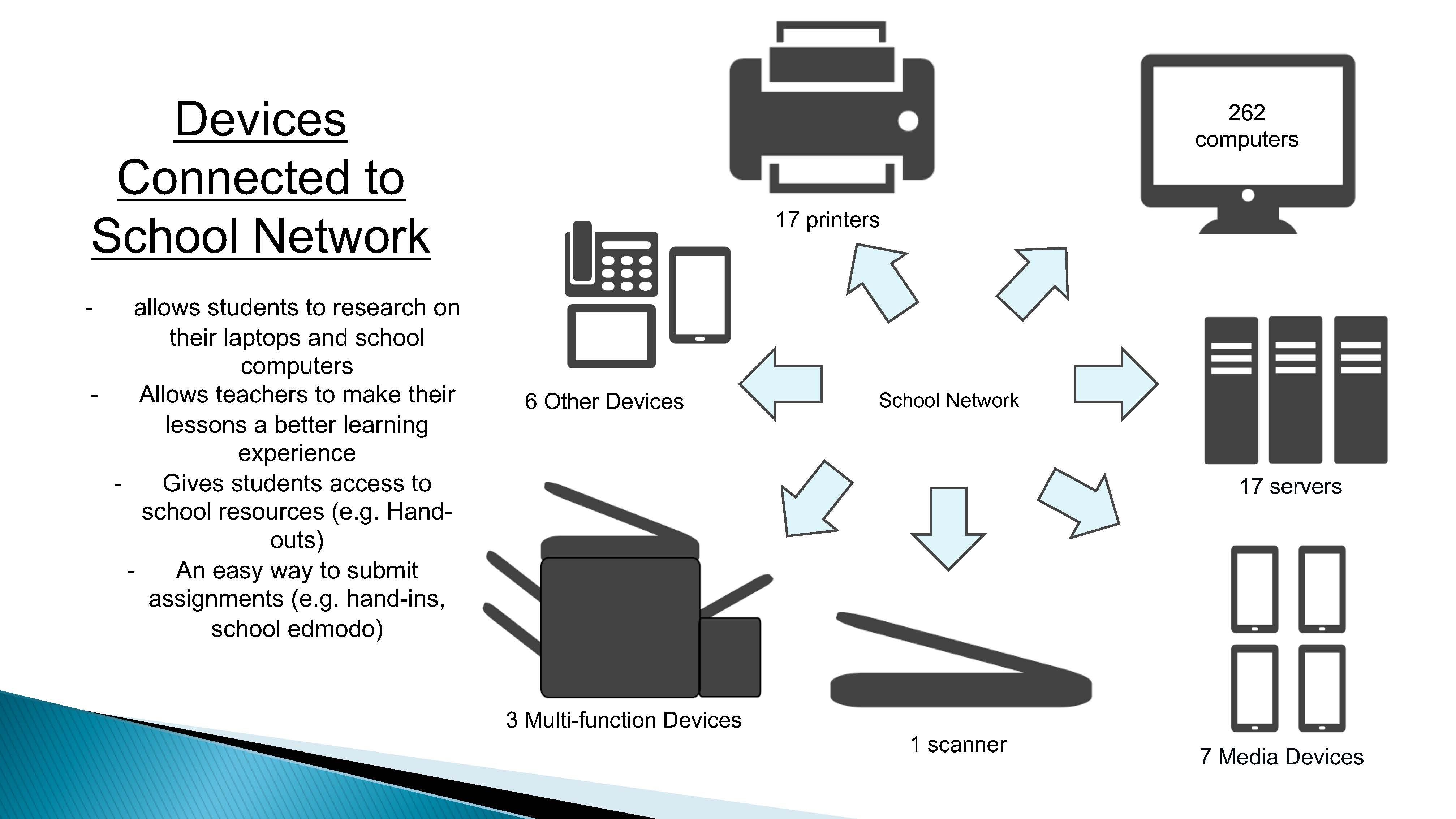
Identifies general purpose of the school network and lists hardware components
-
Annotations
-
1
Annotation 1
Identifies general purpose of the school network and lists hardware components
 1
Annotation 1
1
Annotation 1
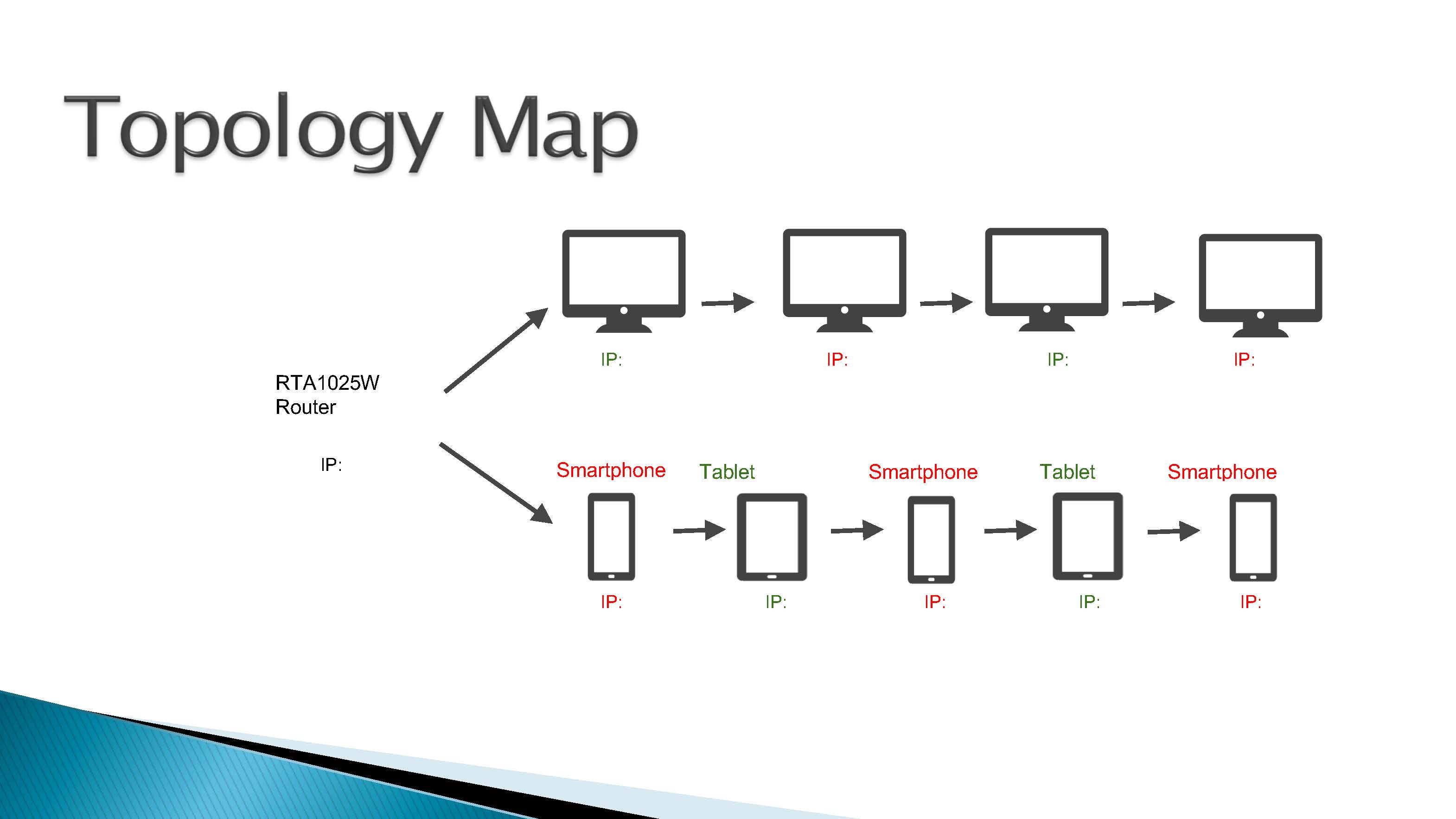
Creates a diagram that suggests multiple devices are connected in some way
-
Annotations
-
1
Annotation 1
Creates a diagram that suggests multiple devices are connected in some way
 1
Annotation 1
1
Annotation 1
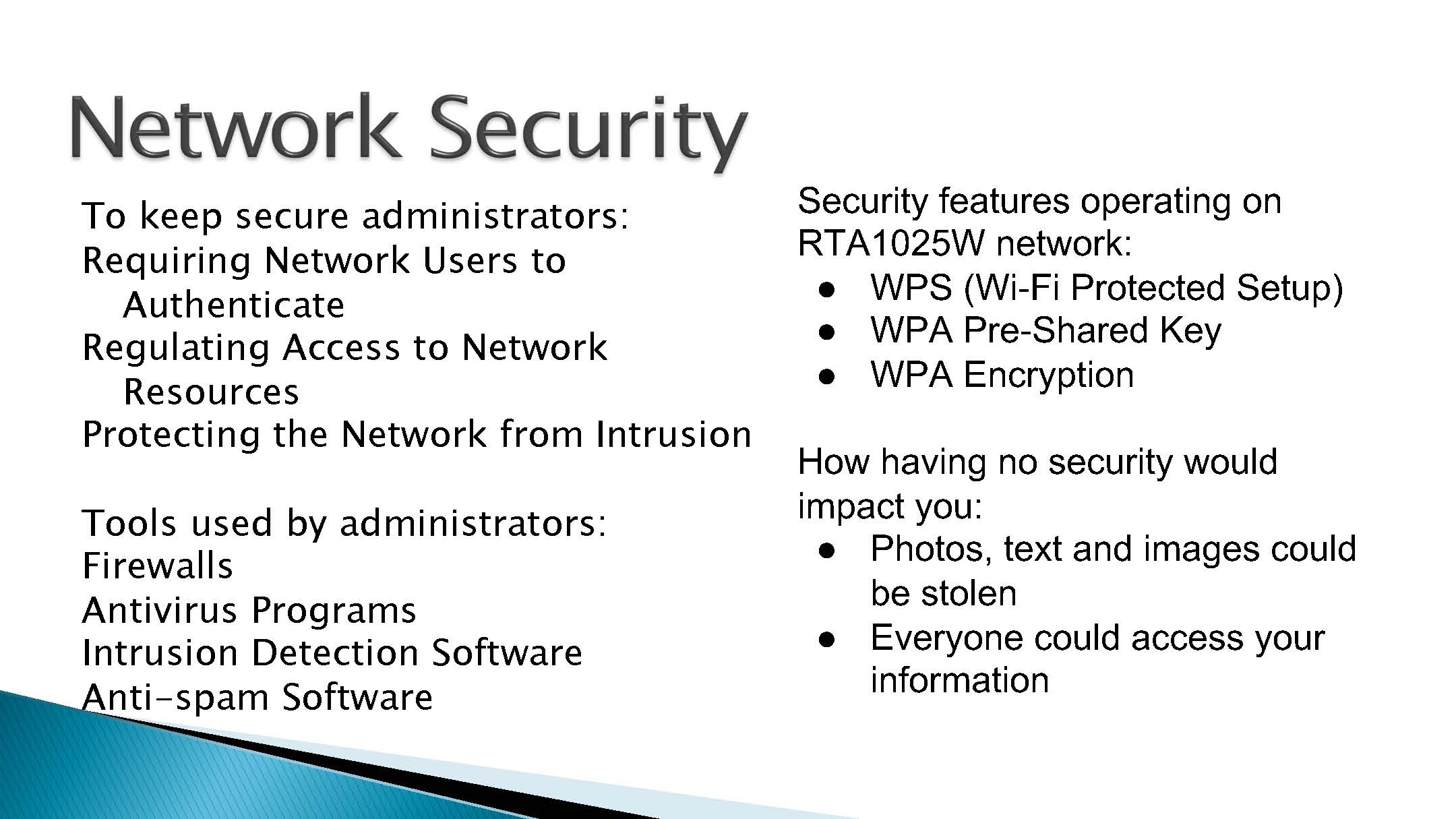
Lists a range of network security features
-
Annotations
-
1
Annotation 1
Lists a range of network security features
 1
Annotation 1
1
Annotation 1
Demonstrates limited knowledge of terminology related to data transmission
-
Annotations
-
1
Annotation 1
Demonstrates limited knowledge of terminology related to data transmission
 1
Annotation 1
1
Annotation 1
Identifies correctly how hardware is linked together on a network
-
Annotations
-
1
Annotation 1
Identifies correctly how hardware is linked together on a network
 1
Annotation 1
1
Annotation 1
Describes the visual representation only of a bus topology 2 Annotation 2
States the topology selected and two possible benefits
-
Annotations
-
1
Annotation 1
Describes the visual representation only of a bus topology -
2
Annotation 2
States the topology selected and two possible benefits
 1
Annotation 1
1
Annotation 1
Draws a simple line drawing of the relationship between components
-
Annotations
-
1
Annotation 1
Draws a simple line drawing of the relationship between components
Satisfactory
Investigation: Secure networks


 1
Annotation 1
1
Annotation 1
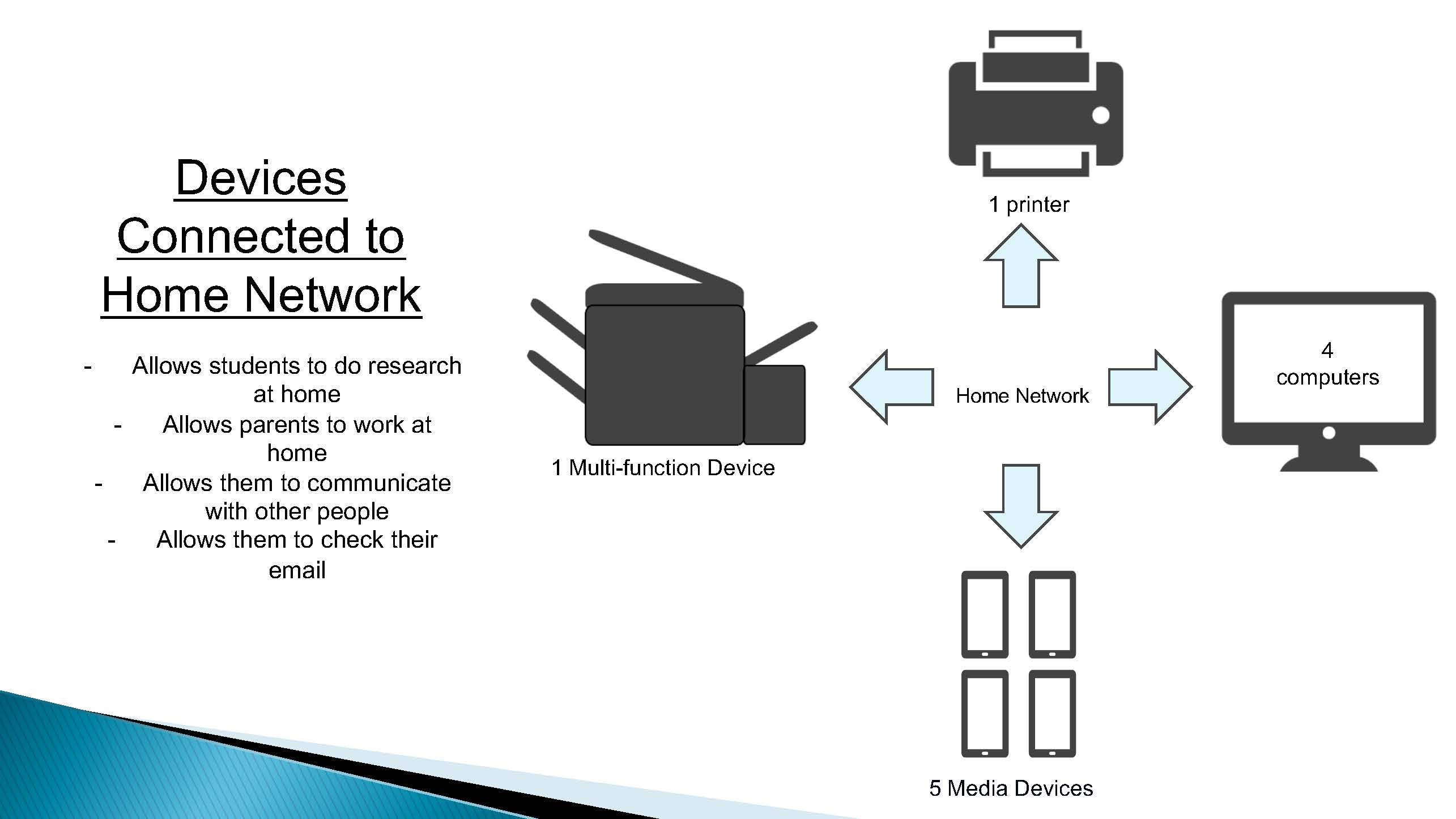
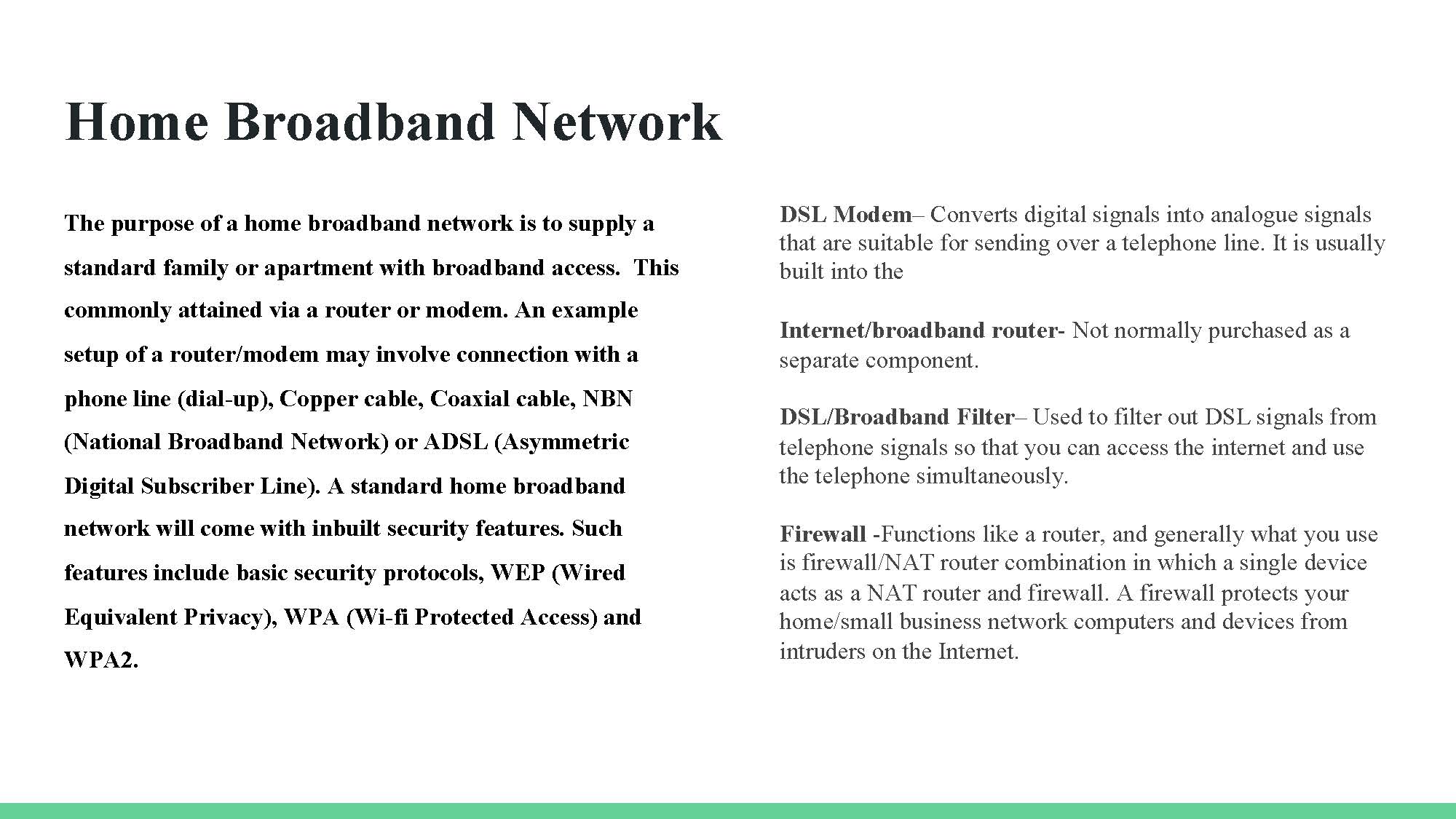
Describes the purpose and main components of a home broadband network
-
Annotations
-
1
Annotation 1
Describes the purpose and main components of a home broadband network
 1
Annotation 1
1
Annotation 1
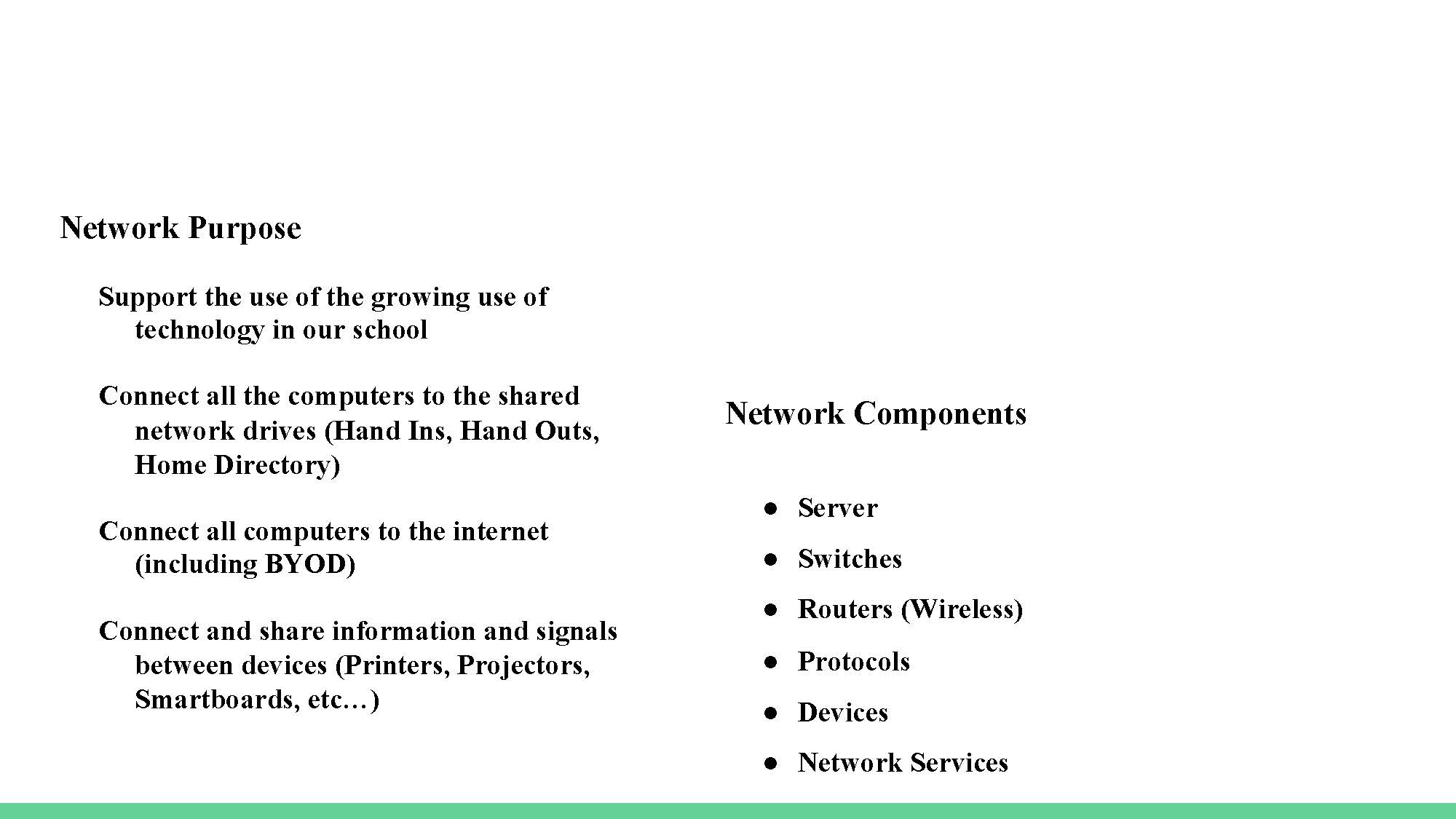
Identifies the purpose of the school network and its main components
-
Annotations
-
1
Annotation 1
Identifies the purpose of the school network and its main components
 1
Annotation 1
1
Annotation 1
Creates a diagram to illustrate the topology of the school network showing the interactions between different hardware components
-
Annotations
-
1
Annotation 1
Creates a diagram to illustrate the topology of the school network showing the interactions between different hardware components
 1
Annotation 1
1
Annotation 1
Explains the purpose of internet protocol (IP) addresses
-
Annotations
-
1
Annotation 1
Explains the purpose of internet protocol (IP) addresses

 1
Annotation 1
1
Annotation 1
Identifies a security feature of the school internet service
-
Annotations
-
1
Annotation 1
Identifies a security feature of the school internet service
 1
Annotation 1
1
Annotation 1
Explains how the security protocol used protects data of different types being transferred
-
Annotations
-
1
Annotation 1
Explains how the security protocol used protects data of different types being transferred
 1
Annotation 1
1
Annotation 1
Explains some possible improvements to security protocols
-
Annotations
-
1
Annotation 1
Explains some possible improvements to security protocols
 1
Annotation 1
1
Annotation 1
Explains clearly the implications to devices and data of poor security protocols
-
Annotations
-
1
Annotation 1
Explains clearly the implications to devices and data of poor security protocols
 1
Annotation 1
1
Annotation 1
Demonstrates some knowledge of correct terminology related to data transmission
-
Annotations
-
1
Annotation 1
Demonstrates some knowledge of correct terminology related to data transmission
 1
Annotation 1
1
Annotation 1
Responds appropriately to most types of interactions (hardware, software and user)
-
Annotations
-
1
Annotation 1
Responds appropriately to most types of interactions (hardware, software and user)
 1
Annotation 1
1
Annotation 1
Identifies correctly how hardware is linked together on a network 2 Annotation 2
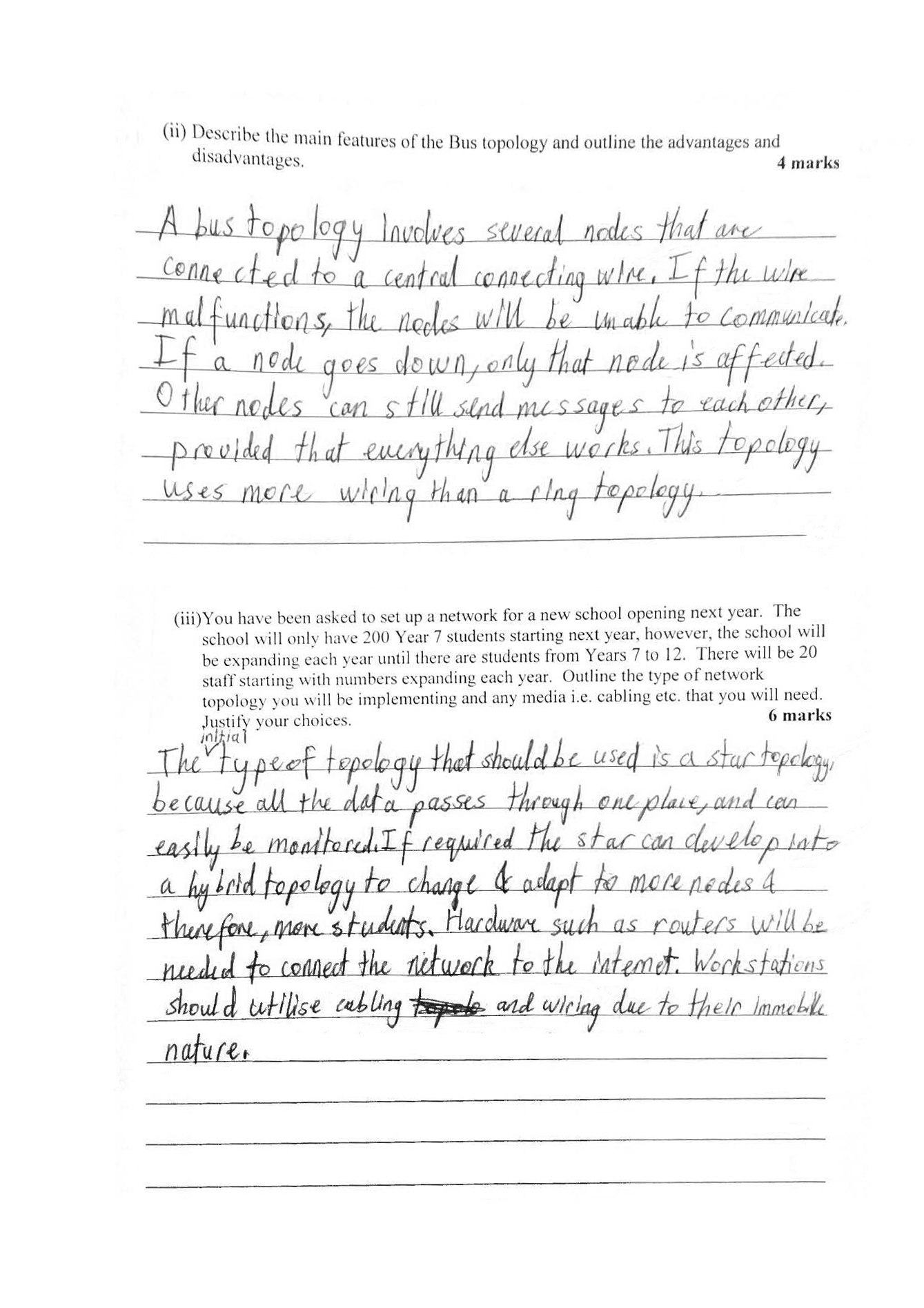
Describes the main features of a star topology and identifies some advantages and disadvantages
-
Annotations
-
1
Annotation 1
Identifies correctly how hardware is linked together on a network -
2
Annotation 2
Describes the main features of a star topology and identifies some advantages and disadvantages
 1
Annotation 1
1
Annotation 1
Describes the main features of a bus topology and identifies some advantages and disadvantages 2 Annotation 2
Explains the appropriate choice of topology based on network purpose, future need and hardware specifications
-
Annotations
-
1
Annotation 1
Describes the main features of a bus topology and identifies some advantages and disadvantages -
2
Annotation 2
Explains the appropriate choice of topology based on network purpose, future need and hardware specifications
 1
Annotation 1
1
Annotation 1
Draws a diagram of a hybrid network featuring elements of star and bus topology
-
Annotations
-
1
Annotation 1
Draws a diagram of a hybrid network featuring elements of star and bus topology
Above satisfactory
Investigation: Secure networks
 1
Annotation 1
1
Annotation 1
Identifies key differences and similarities between the home local area network (LAN) and the school system wide area network (WAN)
-
Annotations
-
1
Annotation 1
Identifies key differences and similarities between the home local area network (LAN) and the school system wide area network (WAN)
 1
Annotation 1
1
Annotation 1
Provides images to illustrate the difference between a LAN and WAN including the interactions between different hardware components
-
Annotations
-
1
Annotation 1
Provides images to illustrate the difference between a LAN and WAN including the interactions between different hardware components
 1
Annotation 1
1
Annotation 1
Explains the need for internal management and control hardware, that is, private addressing, and how it allocates addresses
-
Annotations
-
1
Annotation 1
Explains the need for internal management and control hardware, that is, private addressing, and how it allocates addresses
 1
Annotation 1
1
Annotation 1
Identifies a range of security mechanisms and the risks they mitigate
-
Annotations
-
1
Annotation 1
Identifies a range of security mechanisms and the risks they mitigate
 1
Annotation 1
1
Annotation 1
Identifies how data are kept secure on the school network
-
Annotations
-
1
Annotation 1
Identifies how data are kept secure on the school network
 1
Annotation 1
1
Annotation 1
Demonstrates understanding of the concept of the appropriateness of security for a situation, by suggesting how to improve security and identifying the implications of each suggestion
-
Annotations
-
1
Annotation 1
Demonstrates understanding of the concept of the appropriateness of security for a situation, by suggesting how to improve security and identifying the implications of each suggestion
 1
Annotation 1
1
Annotation 1
Explains a range of implications of not taking appropriate security precautions
-
Annotations
-
1
Annotation 1
Explains a range of implications of not taking appropriate security precautions
 1
Annotation 1
1
Annotation 1
Demonstrates knowledge of correct terminology related to data transmission
-
Annotations
-
1
Annotation 1
Demonstrates knowledge of correct terminology related to data transmission
 1
Annotation 1
1
Annotation 1
Demonstrates sound understanding of the interactions between hardware, software and users
-
Annotations
-
1
Annotation 1
Demonstrates sound understanding of the interactions between hardware, software and users
 1
Annotation 1
1
Annotation 1
Identifies correctly how hardware is linked together on a network 2 Annotation 2
Summarises succinctly the main features of a star topology and identifies pertinent advantages and disadvantages
-
Annotations
-
1
Annotation 1
Identifies correctly how hardware is linked together on a network -
2
Annotation 2
Summarises succinctly the main features of a star topology and identifies pertinent advantages and disadvantages
 1
Annotation 1
1
Annotation 1
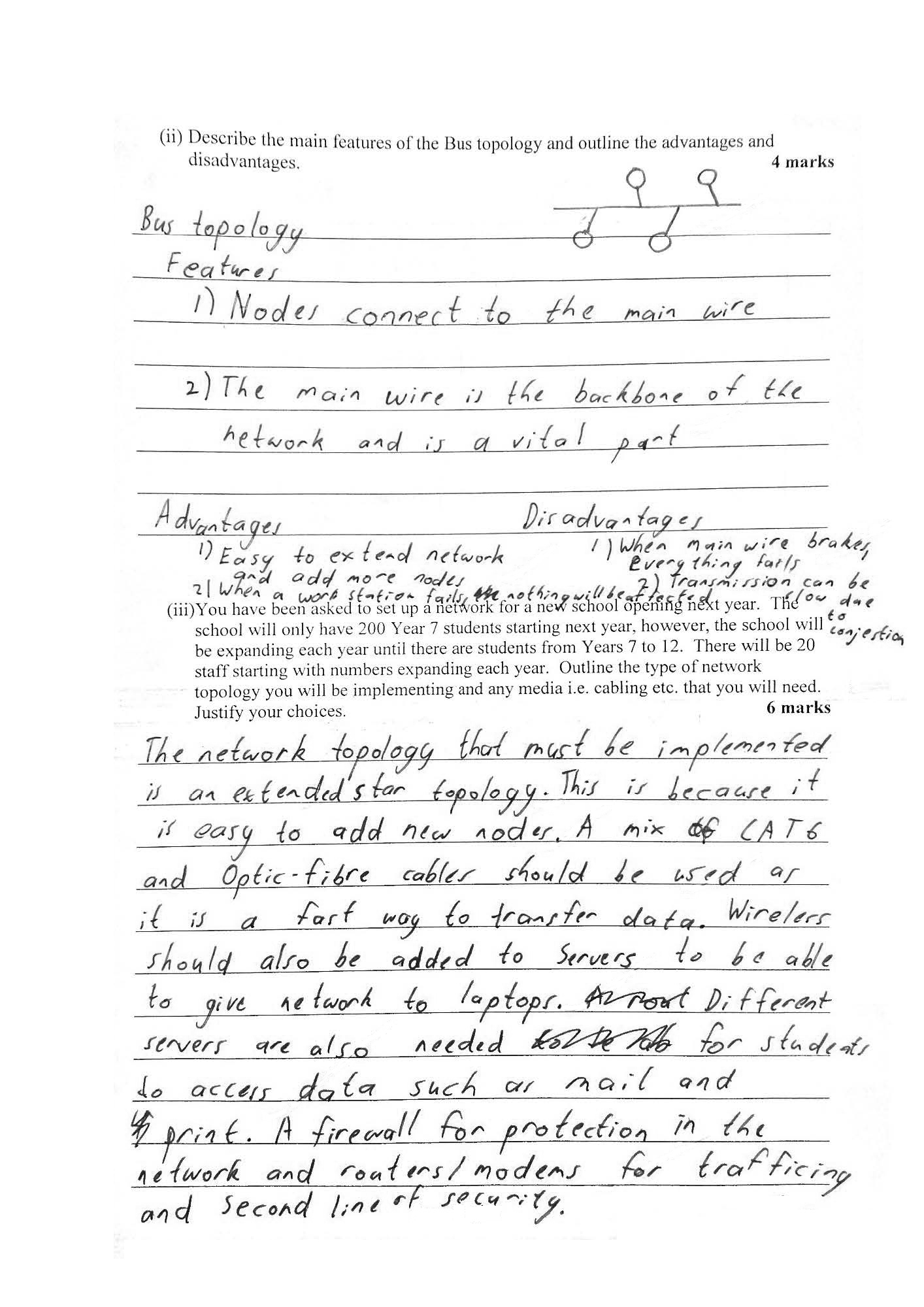
Summarises succinctly the main features of a bus topology and identifies pertinent advantages and disadvantages 2 Annotation 2
Selects and explains appropriate topology including the mix of technologies required that balance both purpose and performance, and allow for growth
-
Annotations
-
1
Annotation 1
Summarises succinctly the main features of a bus topology and identifies pertinent advantages and disadvantages -
2
Annotation 2
Selects and explains appropriate topology including the mix of technologies required that balance both purpose and performance, and allow for growth
 1
Annotation 1
1
Annotation 1
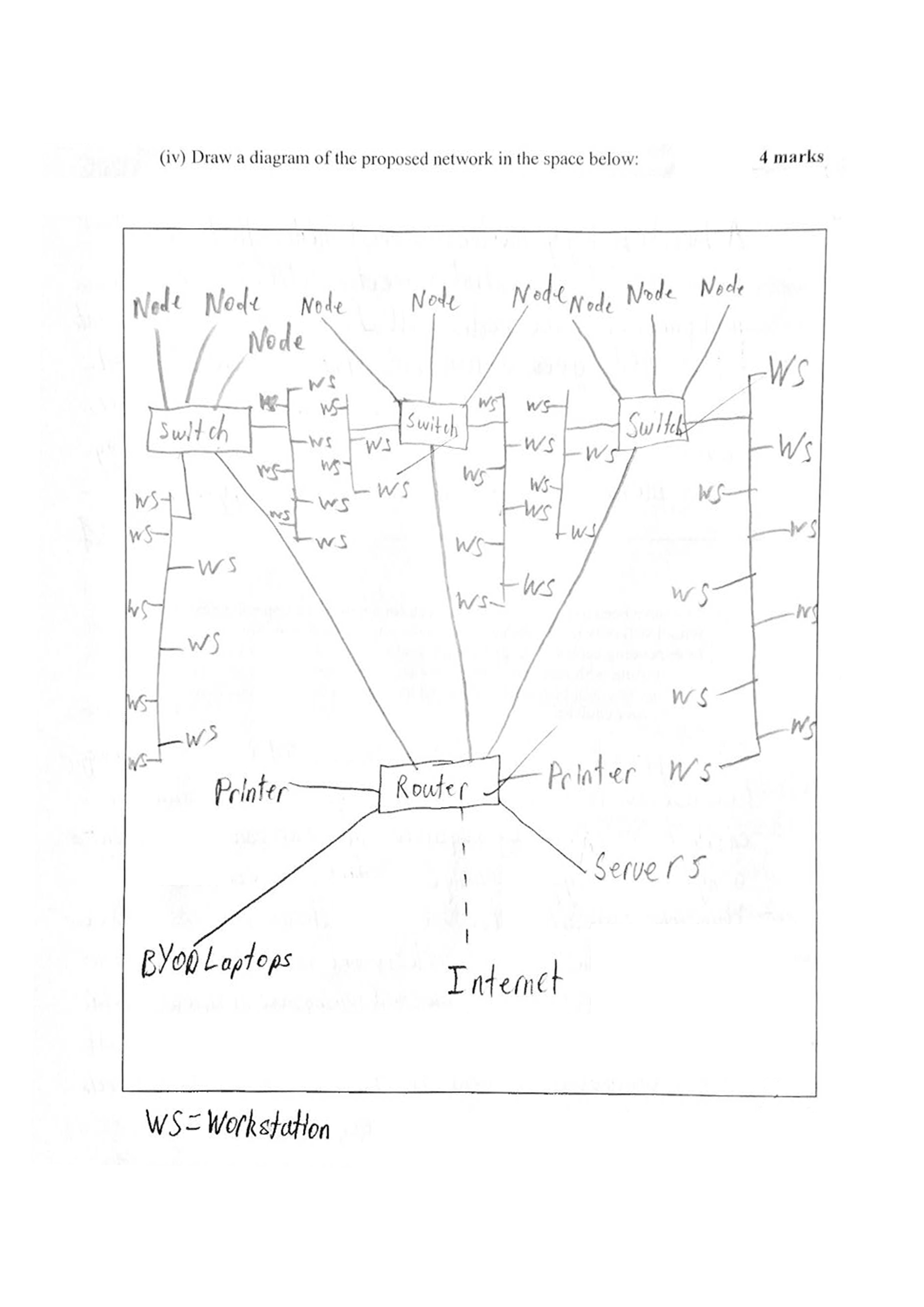
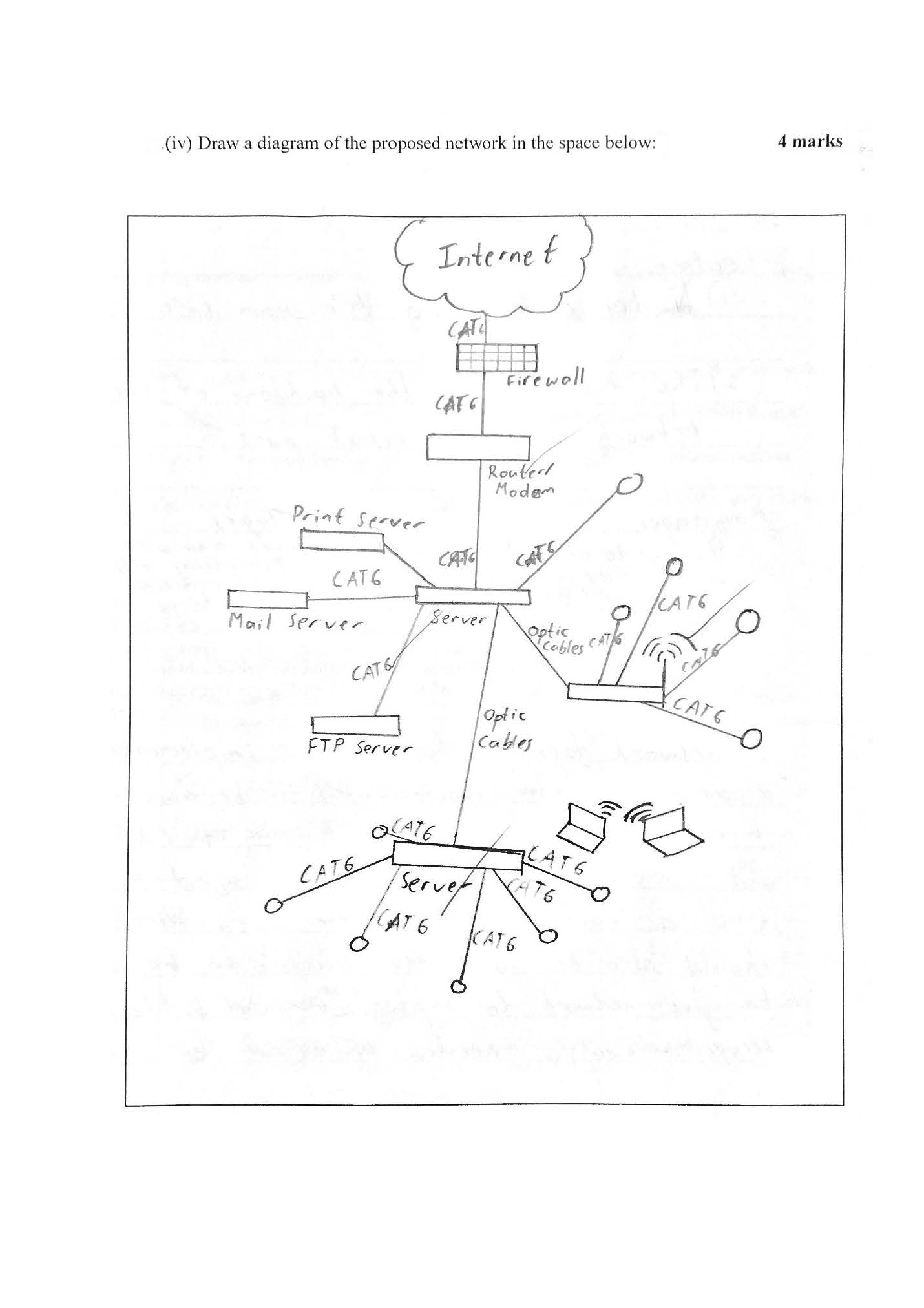
Draws a diagram of an extended star network including a range of connections and using appropriate conventions
-
Annotations
-
1
Annotation 1
Draws a diagram of an extended star network including a range of connections and using appropriate conventions